Hello aspiring Ethical Hackers. In our previous blogpost, you learnt about WiFi Hacking. In this article, you will learn about a different kind of wireless attack called Evil Twin attack. Have you ever used Public Wi-Fi?
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
Nowadays Public Wi-Fi is everywhere. It’s in airports, cafés, coworking spaces, malls, railway stations and hotels. We love it because it’s convenient. Attackers love it because it’s vulnerable. Among the most effective and least-detected wireless attacks today is the Evil Twin Attack, a method where a hacker clones a trusted Wi-Fi network to lure users into connecting. Once connected, victims unknowingly hand over passwords, messages, corporate accounts and even entire session cookies. In this blog post, you’ll learn what an Evil Twin is, how the attack works, the tools used and most importantly how to stay safe from this attack.
What is an Evil Twin Attack?
An Evil Twin is a rogue Wi-Fi access point created by an attacker to impersonate a legitimate wireless network. It uses the same network name (SSID), similar configuration and stronger signal strength to trick users into connecting .
To the victim, it looks like this:
- He visits a cafe, orders a coffee and searches for Wi-Fi.
- He sees a wireless network with SSID “Café_Free_WiFi.”
- He connects to it.
- But unknown to him, he connected to the hacker’s hotspot, not the café’s router.
Now, the hacker can eavesdrop, redirect, modify or steal his data.
How an Evil Twin Attack works?
The Evil Twin attack typically follows a simple lifecycle as shown below.
1. Reconnaissance:
The attacker scans for nearby Wi-Fi networks using tools like:
They identify the target SSID, network channel they are broadcasting on , MAC address and encryption type they are using. For example, let’s say our target SSID is “Shunya”.
2. Creating the Clone:
Next, the attacker sets up a fake access point (Evil Twin) using tools such as:
- hostapd
- airbase-ng
- Wifiphisher
- Fluxion
The Evil Twin broadcasts the same SSID (Shunya) and often uses a stronger signal so the victim’s device automatically prefers it over the original AP.
3. Forcing Disconnections:
Until now, all the new users connectng to original “shunya” may connect to evil twin “shunya”. In some cases, attackers perform deauthentication attacks to disconnect the users already connected to the original “shunya” network. This involves sending deauth packets to connected users, forcing them offline. When victims or his devices try to reconnect, their devices usually choose the Evil Twin because:
- It has a stronger signal.
- It appears identical.
- Devices prefer previously “trusted” SSIDs.
4. Capturing Data:
Once connected to the Evil Twin, the attacker intercepts traffic. Depending on the attacker’s goal, they may:
- Launch a captive portal phishing page to steal passwords.
- Collect WPA/WPA2 handshakes for cracking.
- Perform man-in-the-middle (MITM) interception.
- Steal session tokens (e.g., Gmail, Facebook).
- Redirect to malicious downloads or malware sites.
5. Credential Harvesting:
The most common goal is credential theft. Hackers display fake login pages resembling:
- Office 365
- Google login
- Café Wi-Fi login
- Hotel portals
Once the user enters their password, the attacker immediately receives it. Let’ s see it practically using a tool called Wifiphisher because it’s the simplest one. Our Attacker system is Kali Linux. Wifiphisher can be installed on Kali Linux as shown below.
sudo apt install wifiphisher
Once installation is finished, Wifiphisher can be started using command shown below.
sudo wifiphisher
Wifiphisher starts scanning for nearby wifi networks. Then the tool will prompt you to select the Wi-Fi Access Point of which you want to create an Evil twin as shown below.
For this tutorial as always (OK, most of the time) I will select the Wi-Fi network “Hack_Me_If_You_Can” as my target.
The tool will prompt you the available phishing scenarios available. For this case, OAuth Login Page attack is available.
The OAuth Login Page attack creates a fake login page asking for credentials of the users who want to connect. Note that while creating a fake access point, it is created as an open network unlike the one we are targeting. I select the OAuth Login Page attack and the attack starts. Our Evil Twin is ready.
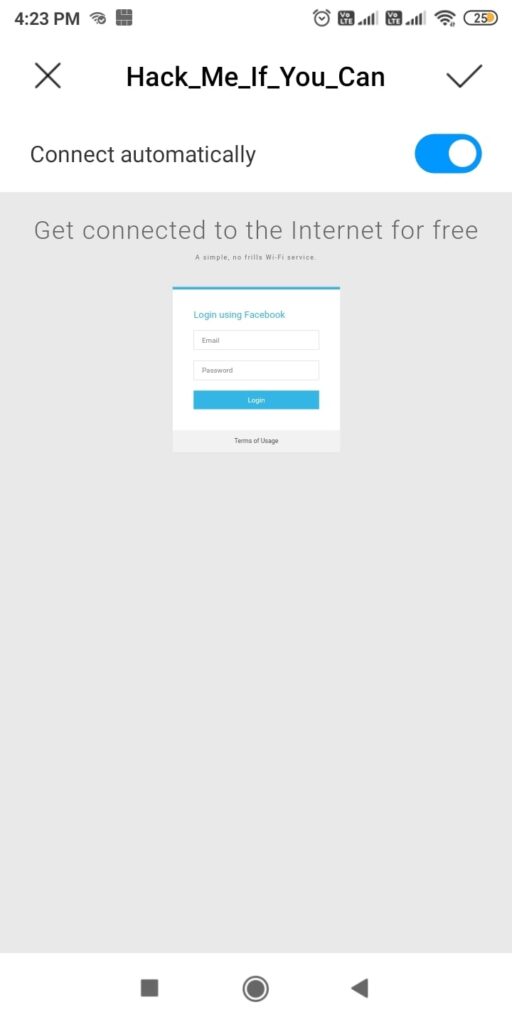
So just imagine while we are running this Fake access point, some mobile user is looking for available Wi-Fi networks to connect to. He will see two networks with the same name and gets confused. Once he selects our Evil Twin to connect to, he will be prompted with a login page as shown below.
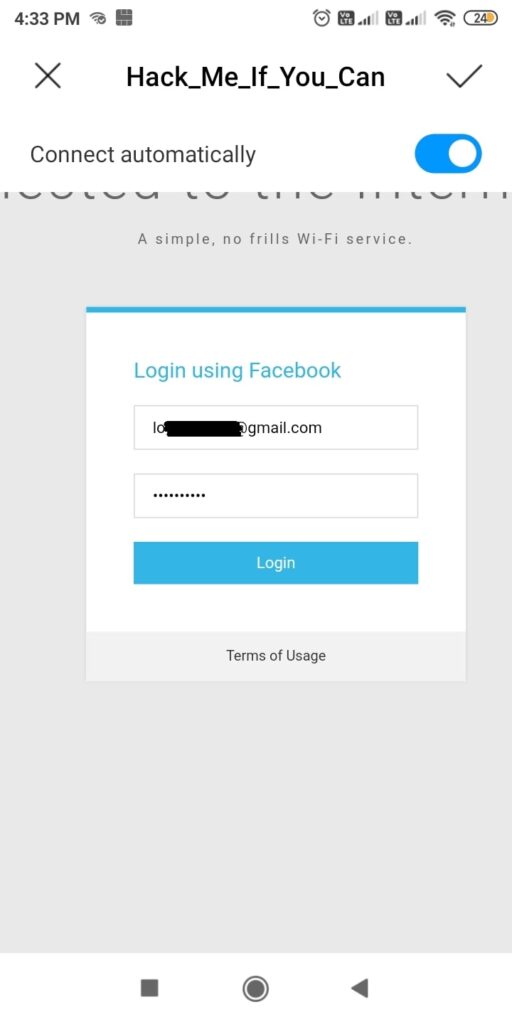
Here, he is being asked to submit his Facebook credentials of course by dangling the carrot of free internet. The login page is so believable even to me. And if the user falls for the trick (or carrot) and submits his credentials as shown below.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
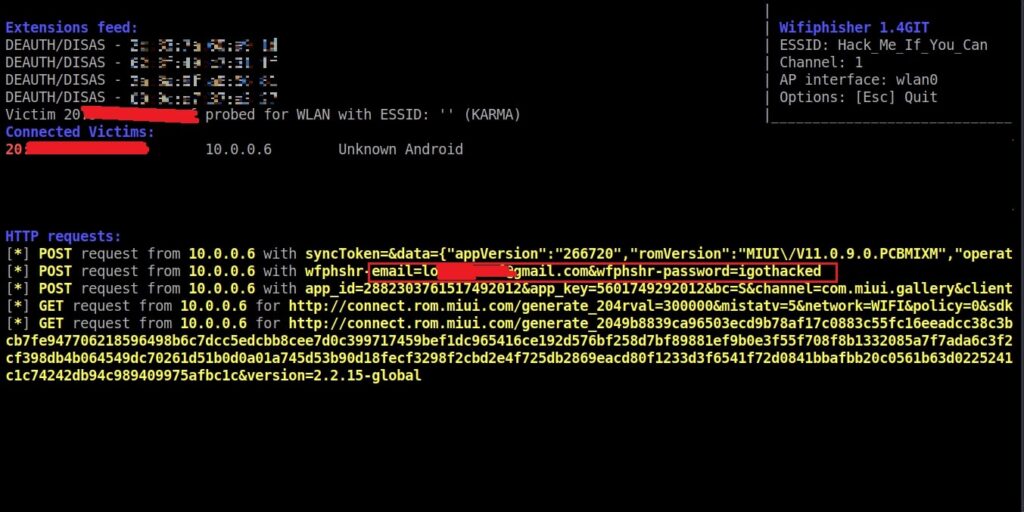
On Kali Linux, the activity is recorded as shown below.
and the credentials are captured successfully.
Why Evil Twin Attacks are so effective?
Evil Twin attacks work because people trust Wi-Fi more than they should. Some reasons include:
Auto-connect Behavior:
Wireless devices automatically connect to familiar wireless network names without verifying legitimacy.
Public Wi-Fi Culture:
Rise of Public Wi-Fi and its usage increases the chances of this attack.
Lack of HTTPS Everywhere:
Although HTTPS is secure and is widely used now, attackers can still:
- Downgrade HTTPS connections
- Redirect traffic
- Harvest non-encrypted requests
- Steal session cookies.
HTTPS Everywhere is not implemented in all cases.
Low Detection by Victims:
Most people cannot differentiate between a real Access Point and its Evil Twin.
Although any Access Point can be targeted with Evil Twin attack, there are a few locations where they are highly probable. These are,
- Airport Wi-Fi: Travelers connect without thinking.
- Corporate Lobbies: Attackers clone the office guest Wi-Fi.
- Coffee Shops: High foot traffic + distracted users.
- Hotels: Many floors, inconsistent signal — perfect for rogue AP placement.
- Tech Conferences: Thousands of users looking for free Wi-Fi.
In several red team assessments, companies discovered that employees connected to rogue Wi-Fi inside their own office buildings — highlighting how devastatingly effective this technique remains.
How to Protect Yourself
1. Avoid Public Wi-Fi for Sensitive of Confidential Tasks:
Never log into banking, email, corporate or other sensitive portals while using a public Wi-Fi.
2. Use a VPN:
A VPN encrypts traffic even over malicious access points like Evil Twins.
3. Turn Off Auto-Connect:
Disable auto-connect for public networks on phones and laptops.
4. Check for HTTPS:
While visiting any website, ensure your browser shows:
- Lock icon
- Valid certificate
- HTTPS
5. Prefer Mobile Hotspots:
Your phone’s hotspot is far safer than unknown public Wi-Fi.
For Companies:
6. Enforce WPA2 Enterprise:
WPA2-Enterprise with certificate-based authentication makes Evil Twin attacks significantly harder.
7. Use a Wireless Intrusion Detection system (WIDS) :
A Wireless Intrusion Detection System (WIDS) detects:
- Rogue Access Points
- Deauth attacks
- SSID spoofing
Evil Twin attacks are simple for attackers to execute but extremely difficult for average users to notice. As long as public Wi-Fi remains popular, this attack vector will continue to be one of the easiest ways for hackers to steal credentials and perform MITM attacks. Security-conscious users and especially cybersecurity professionals must understand how this attack works and adopt strong defensive measures.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply