Hello aspiring Ethical Hackers. In our previous blogpost, you learnt what is enumeration, why it is important and various types of enumeration. In this blogpost, you will learn about SNMP enumeration.
What is SNMP?
SNMP stands for Simple Network Management Protocol. It is a protocol that is used to monitor devices in the network. These devices include routers, switches, bridges, computers and printers etc. This protocol really helpful for organizations with thousands of devices in is network. Learn more about how SNMP works. SNMP contains 3 main components. They are SNMP manager, SNMP agent and Management Information Base (MIB). SNMP runs on UDP ports 161,162.
What information does SNMP enumeration reveal?
SNMP enumeration can reveal information about all the devices on the target network and user accounts on the target system with SNMP server running. Apart from this, SNMP enumeration reveals information about hosts, routers, network information, network interfaces, active TCP and UDP ports on the target system, services running on the network and network shares etc.
How to perform SNMP enumeration?
Simple Network Management Protocol (SNMP) consists of a manager and an agent. Agents are embedded on each and every network device and the manager is installed on a separate computer. SNMP consists of two passwords that are used to access and configure the SNMP agents from the management station. They are, Read community string, Read/write community string.
- Read community string: By default Public, it allows attackers to view device/system configuration.
- Read/write: It is private by default and allows remote editing of configuration.
Tools use these default community strings to extract information about the target. There are many tools that can be used to perform SNMP enumeration. Let’s see one of them.
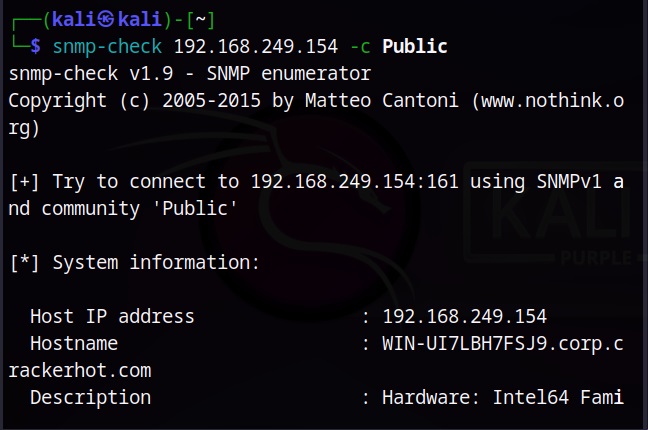
1. snmp-check
SNMP-check is a tool that is installed by default in Kali Linux. Here’s how we can enumerate the default community string of “public” of SNMP.
Here are the user accounts on the target system.
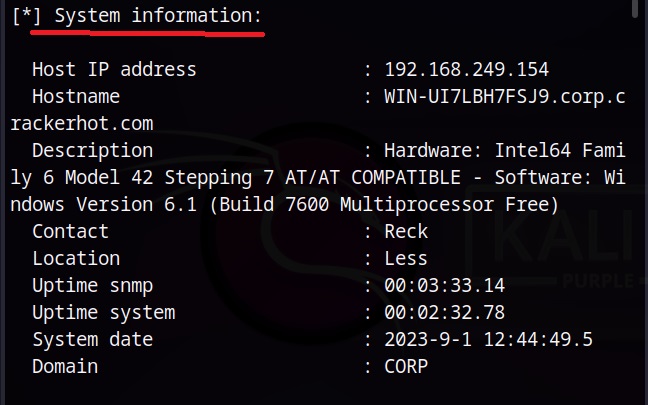
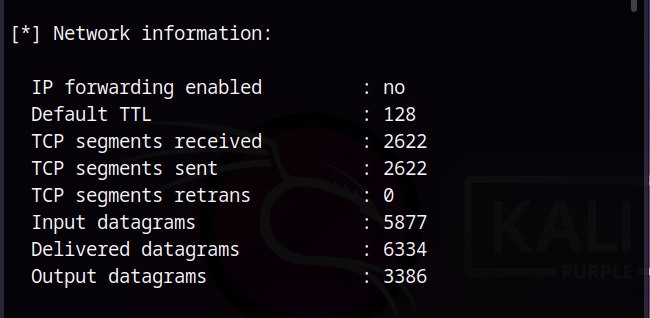
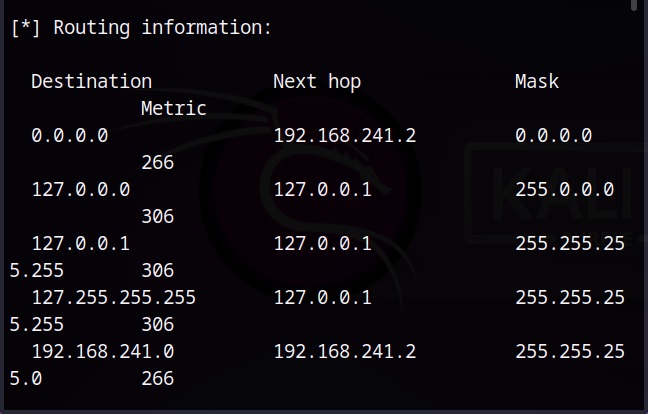
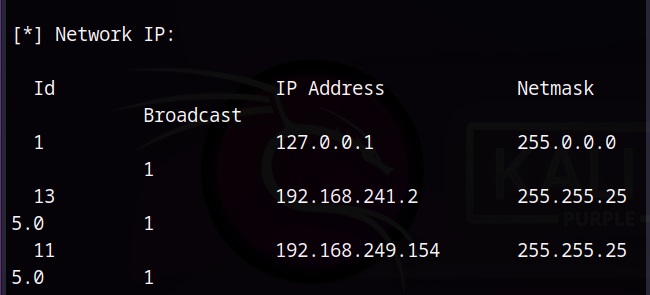
Here the network information is revealed.
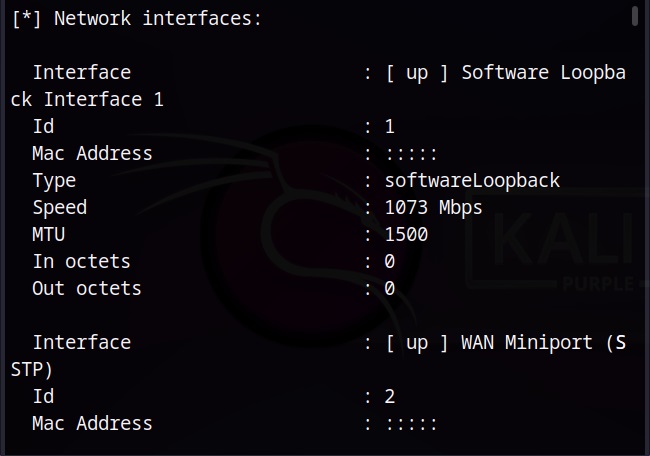
We can see that the target is a Dual-homed system.
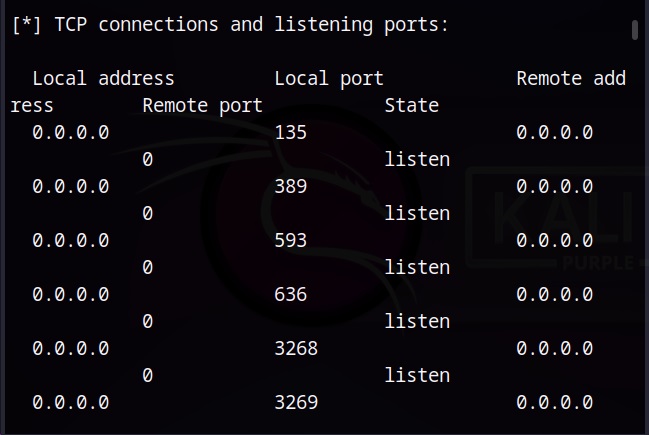
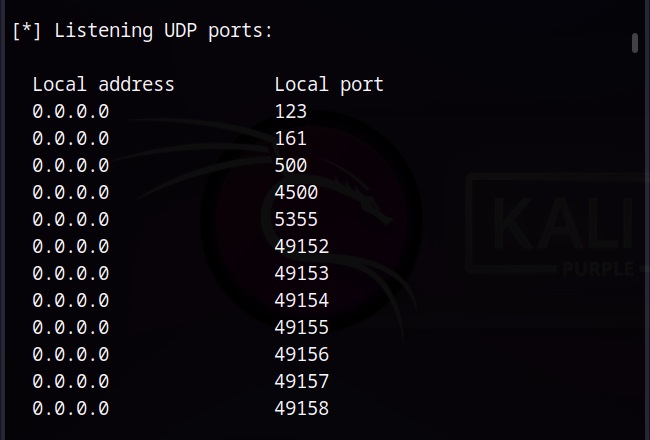
Here are the active TCP and UDP ports.
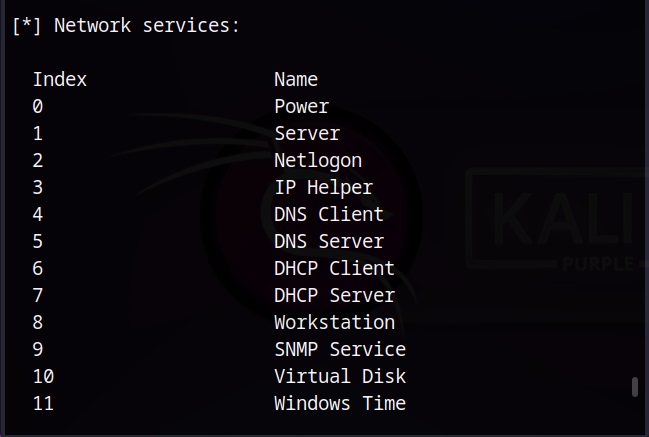
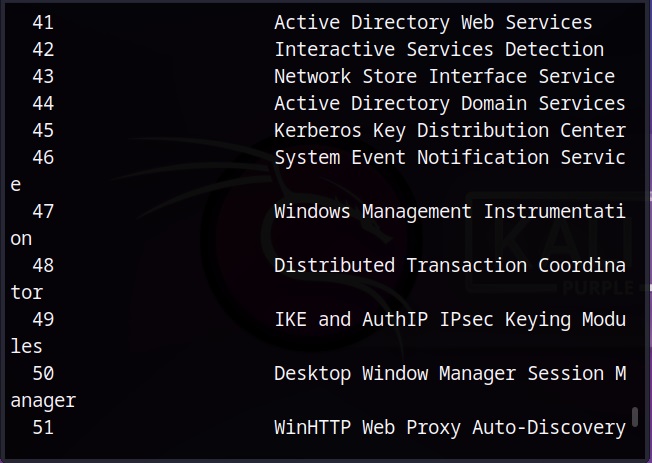
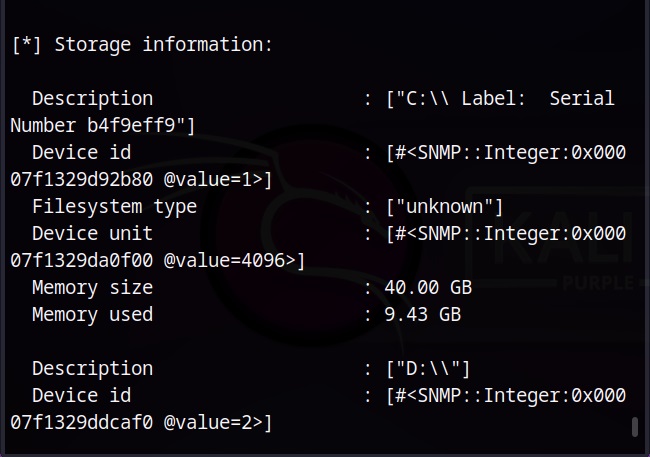
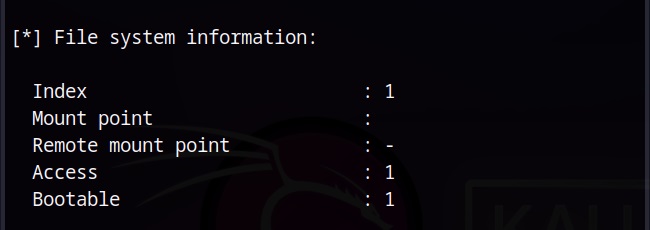
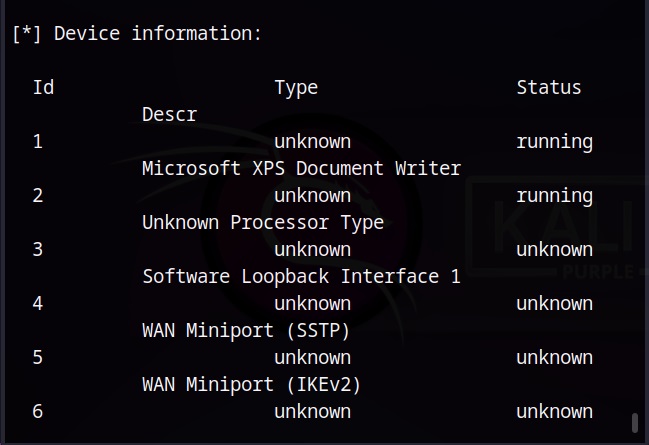
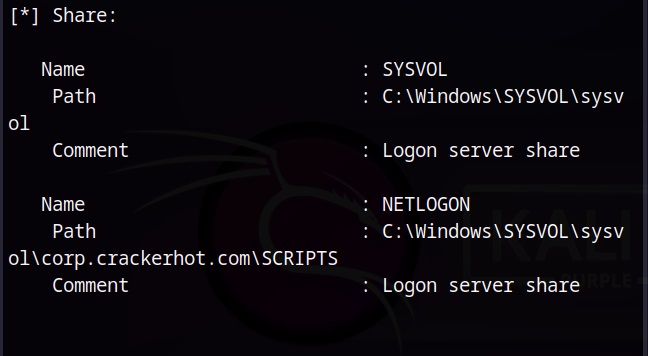
It also reveals other system information about the target.
You can see that SNMP enumeration reveals a lot of information about the target system and network which can prove very helpful as the hack progresses.