If you’re interested in ethical hacking, penetration testing is one of the most exciting paths you can explore. The idea of legally testing systems, finding vulnerabilities and helping organizations improve security sounds exciting and it is.
But many beginners make one mistake: They jump straight into tools without understanding the process.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
Penetration testing is not about randomly running tools. It’s a structured security assessment that combines technical knowledge, methodology and careful analysis. This beginner-friendly guide will help you understand what penetration testing is, how it works, what skills you need and how to start learning it step by step.
What is Penetration Testing?
Penetration testing (often called pentesting) is the process of simulating cyber attacks on systems, applications or networks, with permission to identify security weaknesses. A penetration tester acts like an attacker but with a defensive goal.
Their job is to:
- Find vulnerabilities
- Test security controls
- Assess risk
- Report findings
- Help improve security
In simple terms, Penetration testing is ethical hacking performed in a structured and authorized way.
Why Learn Penetration Testing?
Penetration testing is a highly valuable cybersecurity skill. Here’s why many beginners choose this path.
High Demand:
Organizations need security professionals who can identify vulnerabilities and weaknesses before attackers do.
Practical Learning:
Pentesting is hands-on and problem-solving focused. This will interest you.
Career Opportunities:
This path can lead to roles such as:
- Penetration Tester
- Security Consultant
- Red Team Operator
- Web Application Tester
Skill Development:
You learn:
- Networking
- Systems
- Web security
- Analysis
- Reporting
Important Legal Reminder
Before going any further, let me remind you. Never test systems without authorization. Only practice on:
- Home labs
- Practice environments
- Vulnerable training platforms
- Systems you own
Ethical hacking is always about permission.
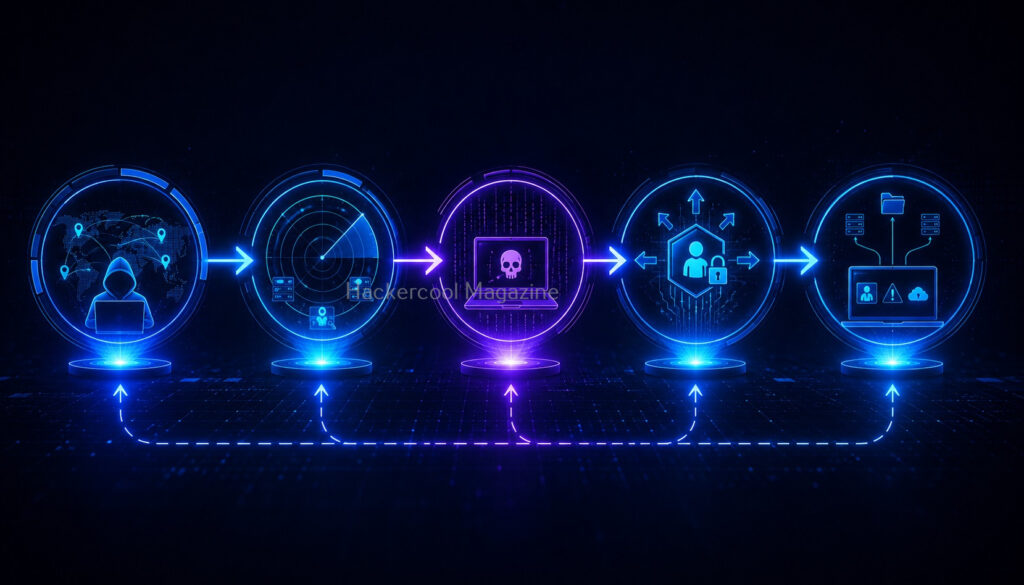
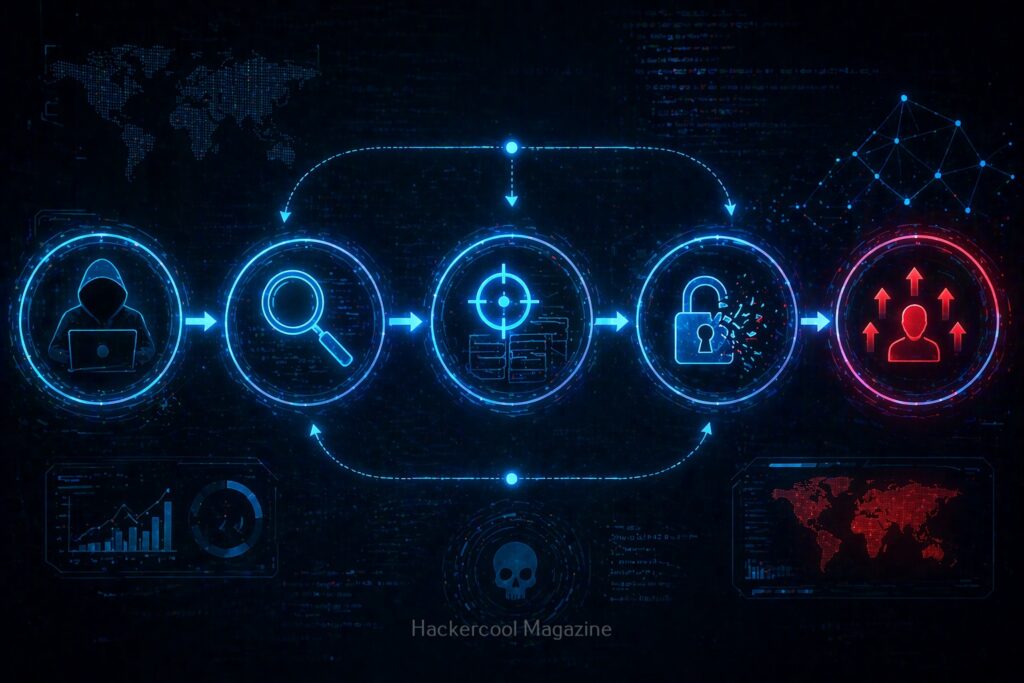
Understanding the Penetration Testing Process
A penetration test usually follows a structured workflow. Let’s break it down.
1. Planning & Scope Definition:
Before testing begins, the scope of the test must be defined. This includes:
- What systems are allowed for testing
- Boundaries of pentest
- Rules of engagement
- Timeline
- Objectives
For example, a company may allow testing only of its web application, not its internal network.
Why this matters?
Unauthorized testing creates legal risk.
2. Reconnaissance (Information Gathering):
This is where penetration testers collect information about the target. Common goals of this stage include:
- Discovering domains
- Identifing IP addresses
- Finding subdomains
- Learn about technologies in use
- Understanding attack surface
This stage helps testers understand what they’re dealing with before interacting further. Think of it as a digital investigation.
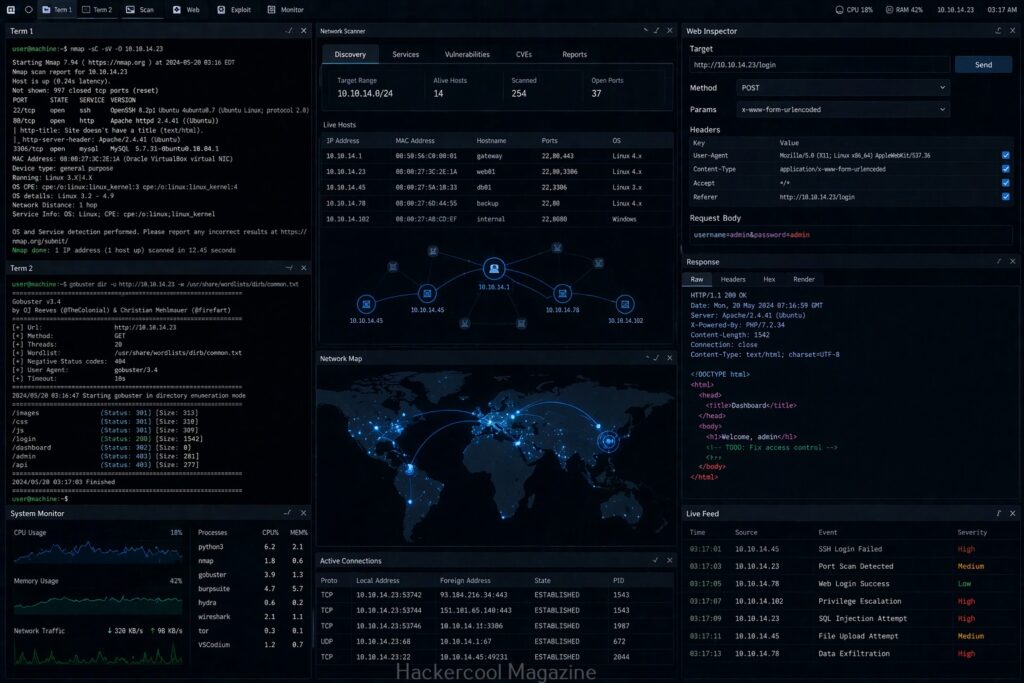
3. Scanning & Enumeration:
Now, the tester actively analyzes systems. This stage focuses on identifying:
- Live hosts
- Open ports
- Running services
- Application endpoints
- Network behavior
Examples:
- Web server detection
- Remote access identification
- Service fingerprinting
This creates a technical map of the environment.
4. Vulnerability Analysis:
After gathering information, the next step is identifying weaknesses. Examples of vulnerabilities and weaknesses are,
- Outdated software
- Weak configurations
- Exposed services
- Common application flaws
This is where analysis matters more than automation. Tools may help but human thinking is critical.
5. Exploitation:
This phase tests whether vulnerabilities can actually be used in testing. Important thing is that this should be done in controlled, authorized environments. The goal is not destruction. The goal is validation.
Examples:
- Confirming access weaknesses
- Testing insecure authentication
- Demonstrating business impact
Sometimes initial access is limited. A tester may assess whether greater access could be achieved.
Examples:
- Moving from limited access to administrative access
- Identifying weak privilege boundaries
This helps determine the severity of issues.
7. Post-Exploitation Analysis:
This stage examines what an attacker could potentially do after gaining access. Questions include:
- What sensitive data might be reachable?
- Could movement between systems occur?
- What would the real impact be?
This helps organizations understand risk.
8. Reporting:
This is one of the most important parts of penetration testing. A great pentester doesn’t just find problems. They communicate them clearly. A penetration test report typically includes:
- Findings
- Risk levels
- Evidence
- Business impact
- Remediation recommendations
Technical skilla alone are not enough. Communication matters.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Skills Beginners Need Before Pentesting
Penetration testing builds on foundational knowledge. Here’s what beginners should focus on.
Networking Basics:
Learn:
- IP addressing
- DNS
- TCP/UDP
- HTTP/HTTPS
- Routing basics
- Common ports
Without networking, pentesting becomes confusing.
Operating Systems:
Understand:
- Linux command line
- Windows basics
- Permissions
- File systems
- Processes
Most cybersecurity labs rely heavily on Linux familiarity.
Web Application Basics:
Many pentests focus on web apps. Learn:
- HTML
- JavaScript basics
- Client/server communication
- Forms
- Sessions
- Cookies
Security Fundamentals:
Understand:
- Authentication
- Authorization
- Encryption basics
- Common attack concepts
- Defensive controls
Basic Scripting:
You don’t need advanced programming skills immediately. But scripting helps. Python is a strong starting point.
Useful for:
- Automation
- Parsing output
- Learning logic
Beginner-Friendly Practice Environment:
Hands-on learning is essential. A simple lab can include:
- Virtual machines
- Linux environment
- Practice targets
- Browser testing setup
Practice environments help you:
- Learn safely
- Experiment freely
- Build confidence
Common Beginner Tool Categories
Tools support learning but should not replace understanding. Beginners should become familiar with:
Reconnaissance Tools:
Used for information gathering.
Network Analysis Tools:
Used for traffic and connectivity understanding.
Scanning Tools:
Used for identifying systems and services.
Web Testing Tools:
Useful for understanding web application behavior.
Analysis Tools:
Help inspect configurations, responses and artifacts.
Focus on learning categories first, not memorizing dozens of tools.
Common Beginner Mistakes
Avoid these mistakes.
Jumping Straight Into Exploitation:
Many beginners want “hacking” immediately. But skipping fundamentals creates confusion.
Tool Dependency:
Running tools without understanding results is not real pentesting.
Ignoring Reporting Skills:
Technical findings must be communicated clearly.
Practicing on Real Targets:
Unauthorized testing is never acceptable.
Trying to Learn Everything at Once:
Pentesting includes:
- Networking
- Systems
- Web
- Security
- Analysis
Take it step by step.
Beginner Learning Roadmap
Here’s a practiocal learning roadmap for you.
Month 1-2:
Focus on:
- Networking
- Linux basics
- Web fundamentals
Month 3-4:
Learn:
- Reconnaissance concepts
- Network analysis
- Security basics
Month 5-6:
Start:
- Safe practice labs
- Web testing basics
- Traffic analysis
Month 6-9:
Practice:
- Vulnerability identification
- Scenario-based labs
- Documentation
Month 9-12:
Develop:
- Workflow understanding
- Reporting skills
- Specialized interests
Web vs Network Pentesting
Beginners often ask which path to start with. Here are the differences between web pentesting and network pentesting.
Web Pentesting:
Focus is on:
- Websites
- APIs
- Sessions
- Authentication
- Input validation
Often easier for beginners because environments are easier to understand.
Network Pentesting:
Focus is on:
- Hosts
- Services
- Ports
- Internal movement
- Infrastructure
Requires stronger networking knowledge.
For many beginners, Web testing is the easier entry point.
Soft Skills Matter Too
Technical skills alone aren’t enough if you want to be a penetration tester. Pentesters also need soft skills like,
Analytical Thinking:
Understanding clues and patterns.
Curiosity:
Asking yourself questions like, “What else is exposed?”
Patience:
Have patience because testing takes time.
Communication:
Writing useful reports.
Documentation:
Tracking findings properly.
Career Opportunities
Penetration testing can lead to:
- Junior Penetration Tester
- Web Application Security Tester
- Security Consultant
- Red Team Analyst
- Application Security Engineer
Beginners usually start with junior or analyst roles.
Certifications (Optional)
Certifications can help but are not mandatory. Skills matter more than certificates. Start by building practical understanding first.
Conclusion
Penetration testing is one of the most rewarding areas of cybersecurity but it requires discipline.
Remember. Pentesting is not about random hacking. It’s about:
- Process
- Methodology
- Analysis
- Communication
- Ethics
If you build strong fundamentals, practice consistently and stay curious, you can absolutely grow into this field.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply