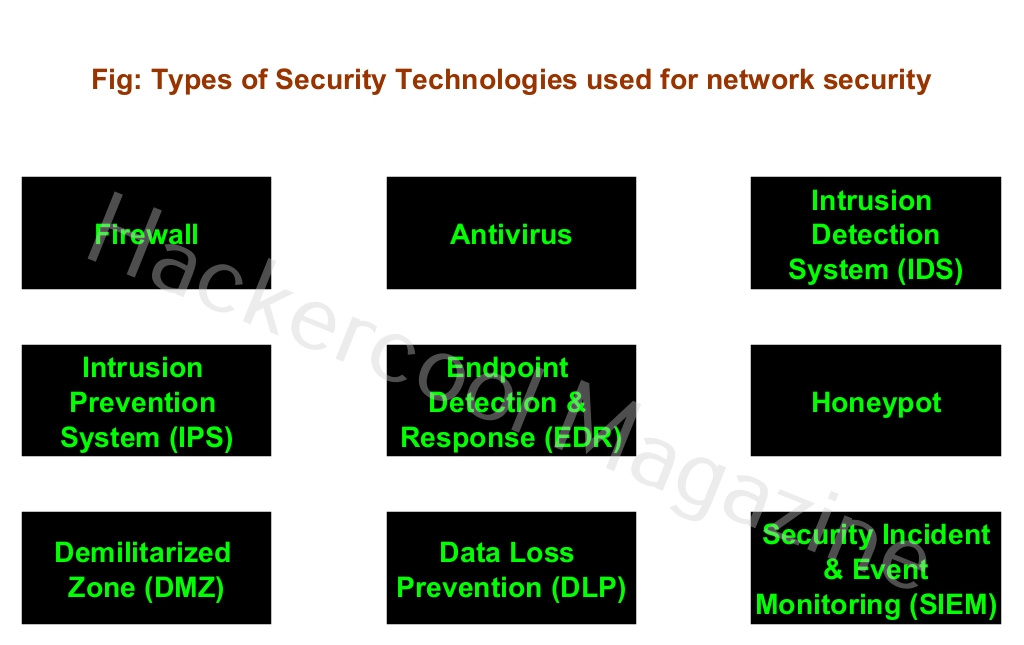
Hello, aspiring Ethical Hackers. In this blogpost, you will learn about different security technologies that are used in an organization to protect the network against cyber-attacks. Various devices and software come into play while protecting the organization from a variety of threats. Let’s learn about each of them.
1. Firewall:
A firewall is the most common defensive measure that is used in organizations against cyber attacks. It can be considered the first layer of defense against hackers. Just as its name implies, it works as a wall between two networks thus preventing malicious traffic from entering the network of the organization. Learn more about firewalls here.
2. Anti-Malware:
In one of our previous articles, you learnt about virus and malware. Anti virus protects the computers and other devices in the network from this malicious software. Learn more about Antivirus.
3. Intrusion Detection System (IDS):
An Intrusion Detection System (IDS) monitors the entire traffic of the network and as soon as it sees any traffic that it considers malicious, it raises an alert. Learn more about IDS.
4. Intrusion Prevention System (IPS):
An Intrusion Prevention System (IPS) is one step above IDS. It performs the functions just like an IDS, but whenever it detects malicious traffic, it tries to prevent the connection by dropping the packets. Learn more about Intrusion Prevention System (IPS).
5. Endpoint Detection & Response (EDR):
Endpoint Detection and Response is used to monitor end user devices on the network for malware and acts against them if needed.
6. Honeypot:
Sometimes, organizations need to understand what hackers would be interested in once they are in their network. A honeypot serves this purpose. A honeypot acts as a juicy target and attracts towards thus preventing them from hacking anything in the original network. A honeypot designed with a lot of vulnerabilities that can keep the hackers constantly interested. Learn more about honeypots.
7. Demilitarized Zone (DMZ):
A demilitarized zone is a network used to add an external layer of security to the organization’s network. Usually placed at the perimeter, it has access to the external network. It usually contains an external facing service.
8. Data-Loss Prevention (DLP):
Data Loss Prevention (DLP) ensures that no confidential data is being sent out of the organization’s network. Confidential data refers to data that once exposed to the internet can harm the security of the network.
9. Security Incident & Event manager (SIEM):
A security Incident & Event Manager raises an alert if it detects any malicious activity. That’s all about the various security technologies.
Follow Us