Those who are first on the battlefield and await the opponents are at ease; those who are last on the battlefield and head into battle get worn out.
SUN TZU, Art Of War.
What is SQL Injection?
Acunetix describes it as ” the type of attack that takes advantage of improper coding of your web applications that allows hacker to inject SQL commands into say a login form to allow them to gain access to the data held within your database. In essence, SQL Injection arises because the fields available for user input allow SQL statements to pass through and query the database directly.
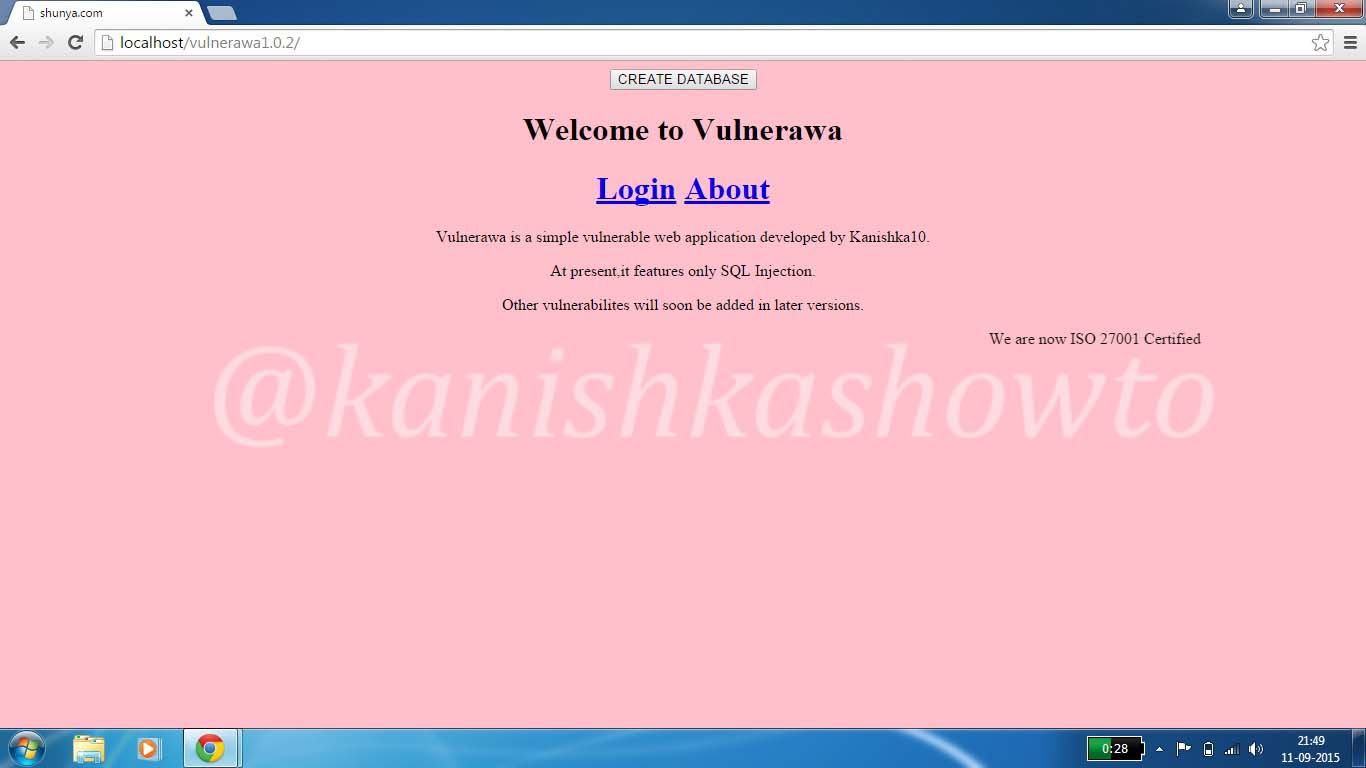
In this howto, I am going to show you how login bypass websites using SQL injection. For this howto, I am going to use Vulnerawa and Wamp server. You can download Vulnerawa from here. To see what is Vulnerawa, go here. To see how to setup vulnerawa in Wamp Server, go here. When you successfully setup Vulnerawa it should be as below. The first page of a website is the “index.php” which is as shown below.
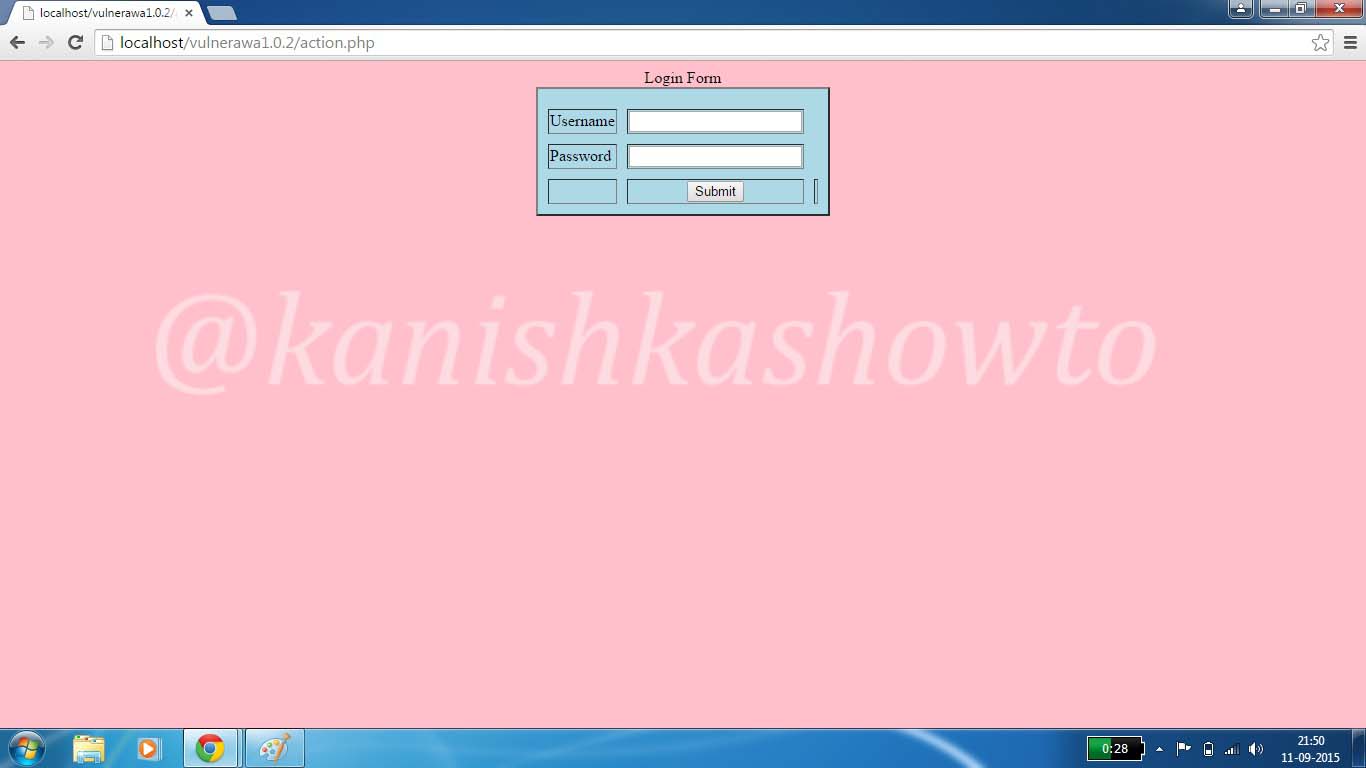
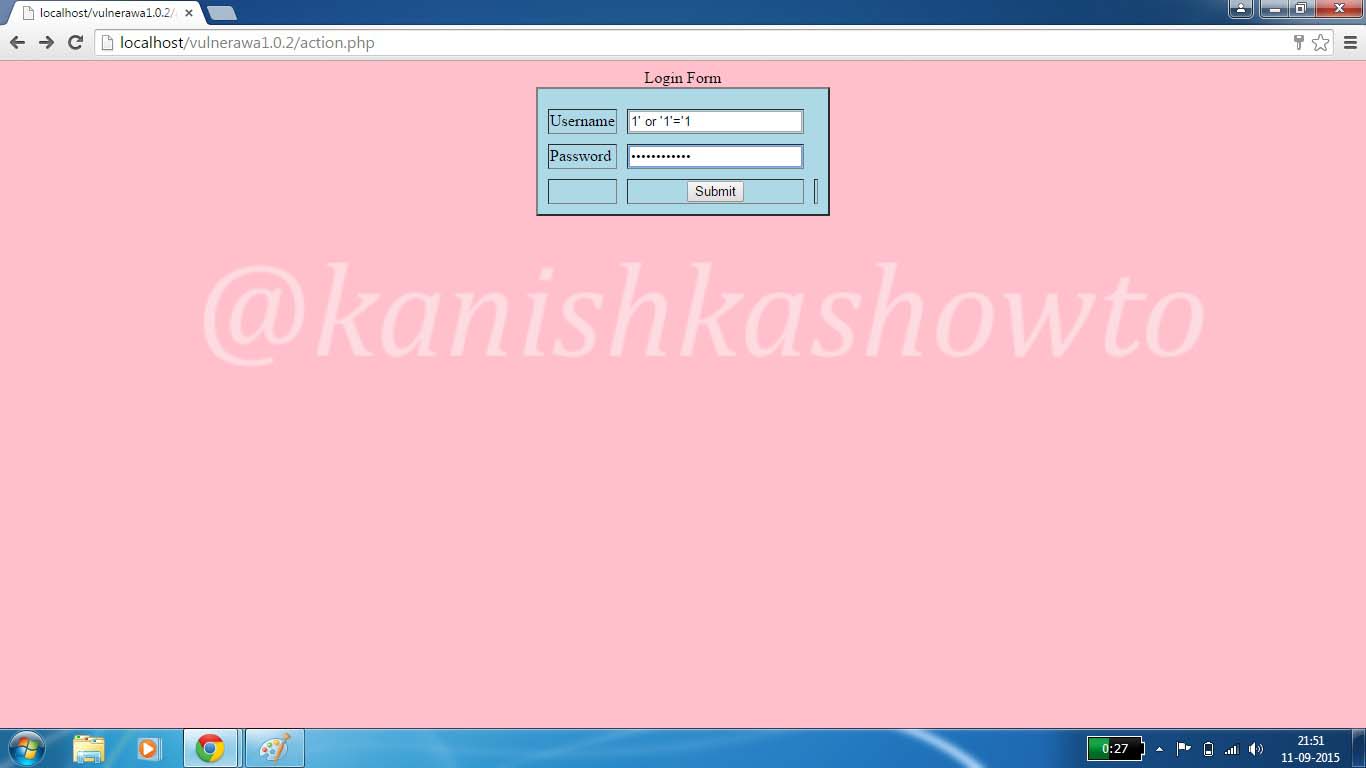
Now click on the “Login” button. You should see a login form as below.
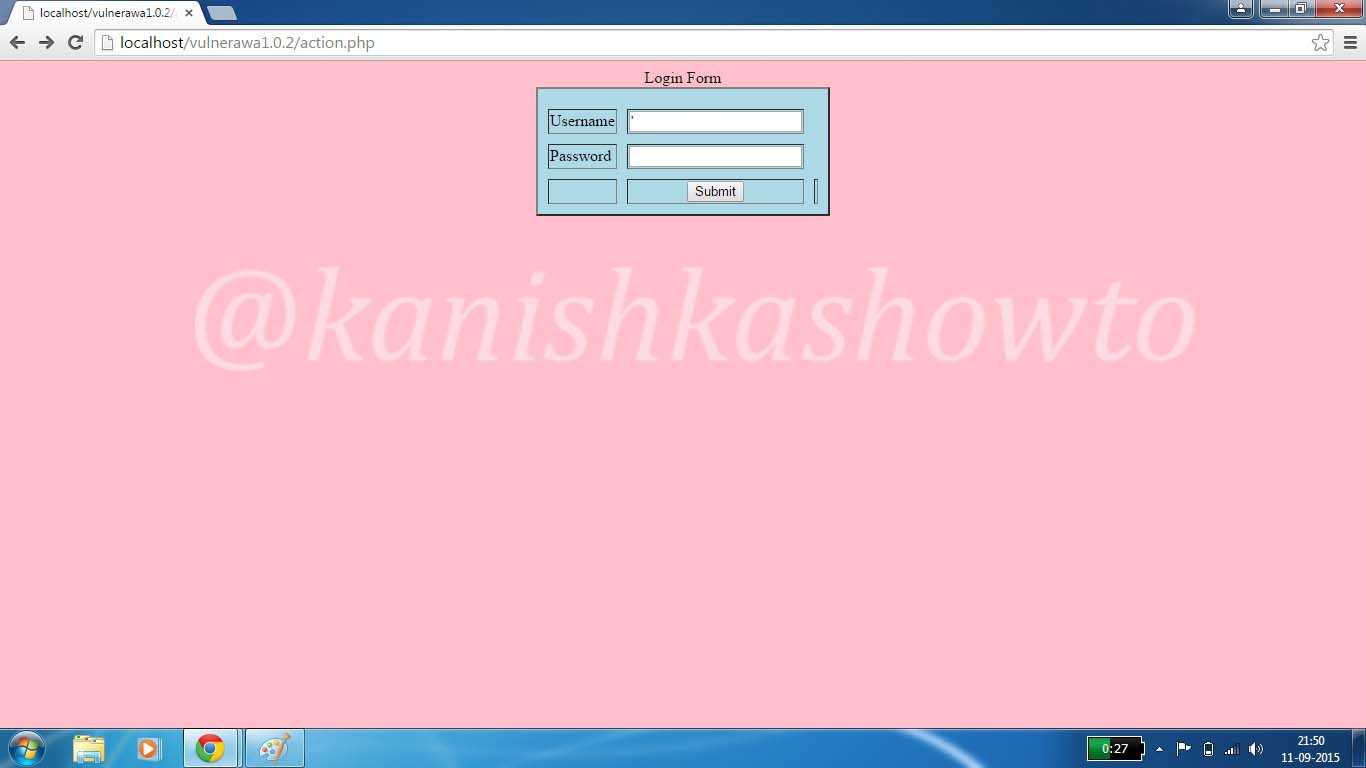
Now insert a single quote character( ‘ ) into the form as shown below.
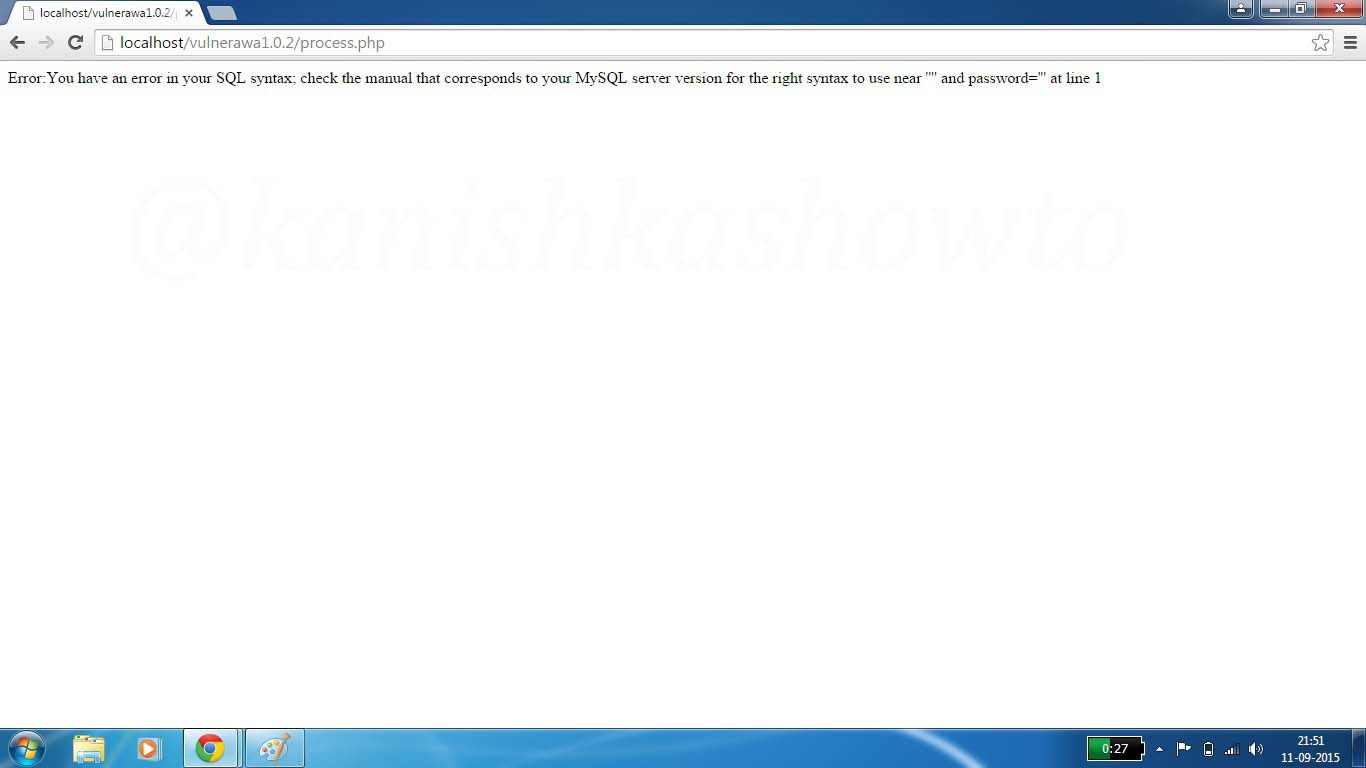
Click on “Submit”. You should get the error as shown below. This shows that the webpage is vulnerable to SQL injection. Notice that the url has changed to a page “process.php”. Remember this for now.
Now enter the query
1′ or ‘1’=’1
as shown below in both username and password fields.
Click on “Submit”. If you got the below webpage, then you have successfully bypassed the login screen.
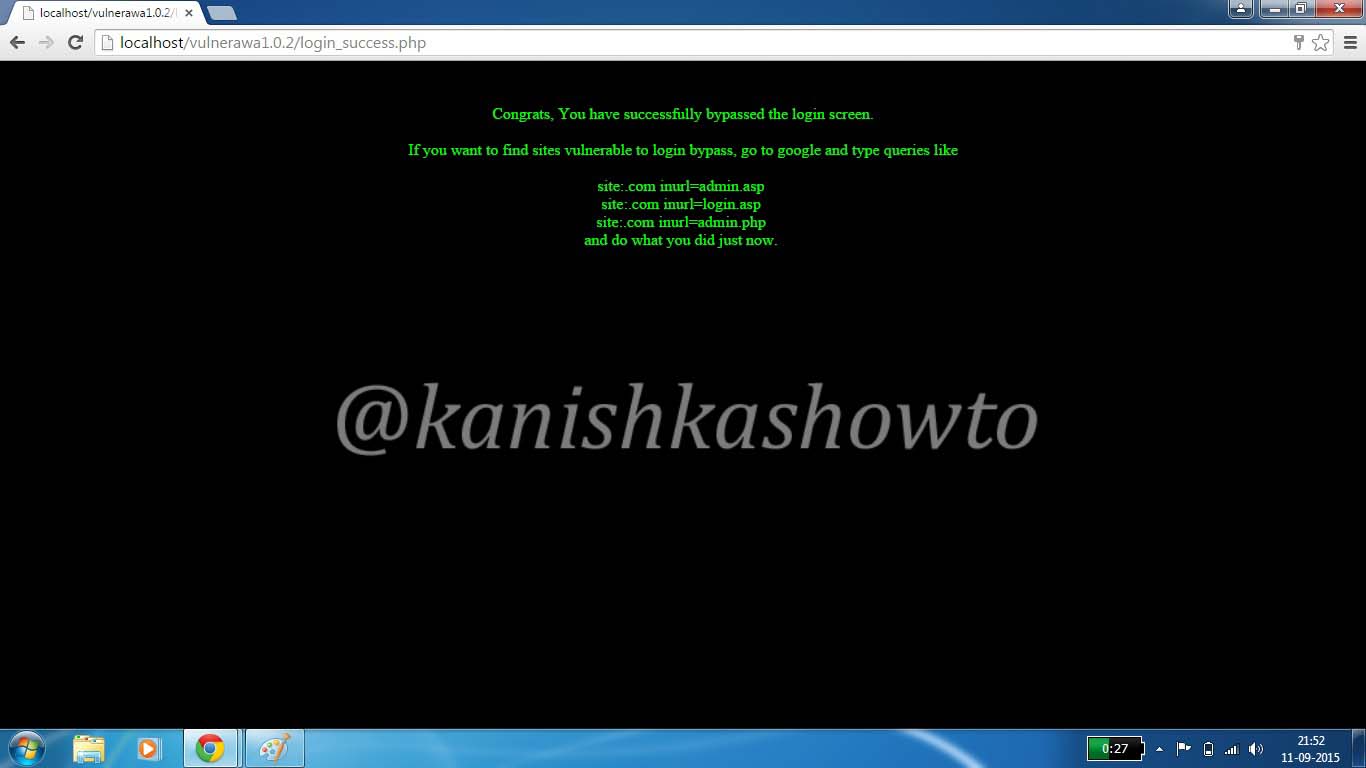
The query we entered above validates the user even without checking the password. There are some other queries which can work similarly. Two of them are here.
‘ or ‘1’=’1;
‘ or ‘1’=’1”
When a hacker enters these two queries, the username field becomes
” or ‘1’=’1;
which transforms to validate the user if username is empty or 1=1. Now whatever may happen, one will always be equal to one. We can find many more using trial and error. This vulnerability exists because we are supplying raw data to our application.
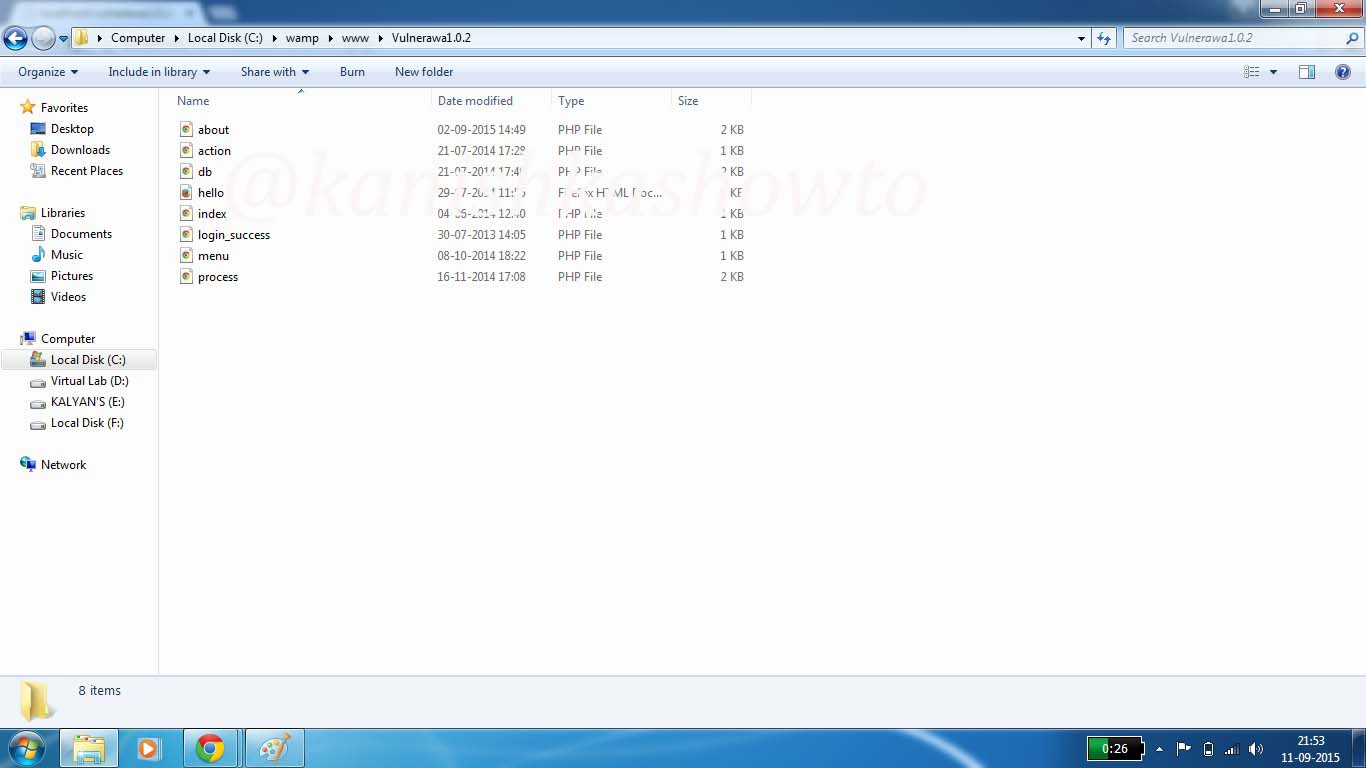
Now let’s go to the page “process.php” to understand how this sql injection worked. Go to the root directory of Vulnerawa. That would be “C://Wamp/www/vulnerawa1.0.2“. You should see the list of below pages. These are all the webpages which make the webapp vulnerawa1.0.2.
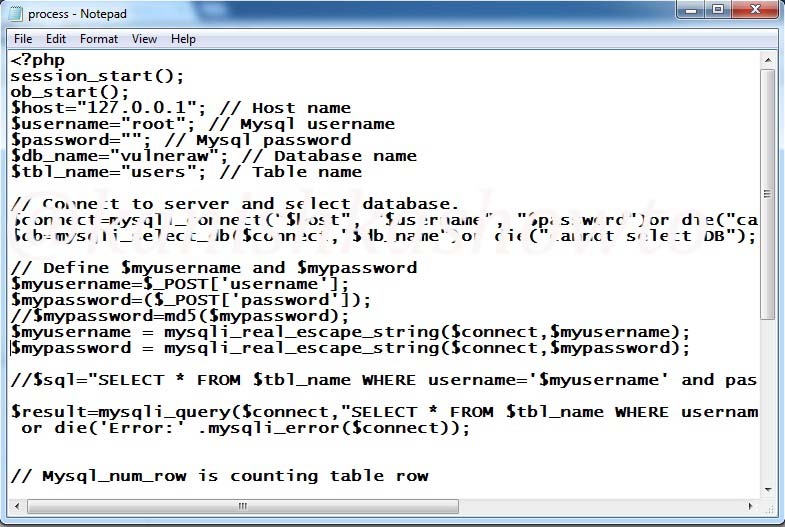
But we are interested in the page process.php. Right click on the page and select “edit” option to view the file. To put simply, open the process.php file with notepad. You should see it as below. We are interested in the two lines of code, $myusername=$_POST[‘username’] and $mypassword=$_POST[‘password’].These are the two queries to take username and password from the user. You can observe that they are taking input directly aka without sanitization.
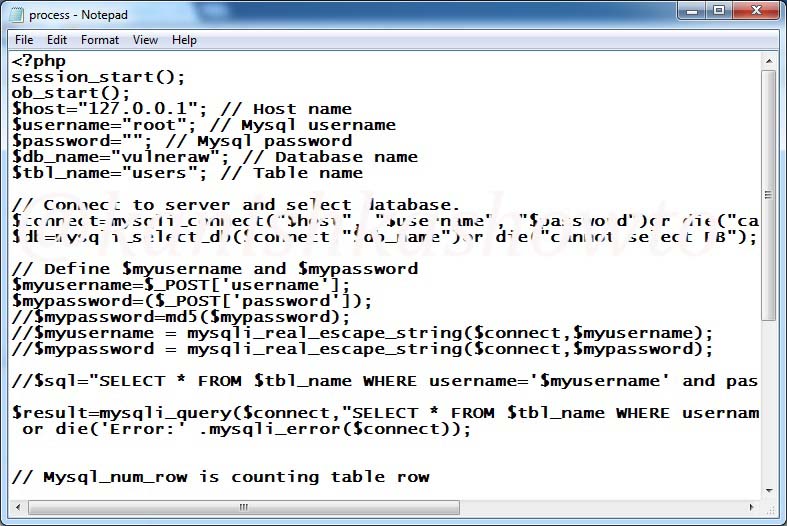
Now just below these two lines, we have two lines commented. These are
$myusername = mysqli_real_escape_string($connect, $myusername);
$mypassword = mysqli_real_escape_string($connect, $mypassword);
Now, uncomment those two lines by removing the two backward slashes as shown below.
Save the file and restart the WAMP server. Now try to bypass the login screen as explained above. You should get something as shown below.
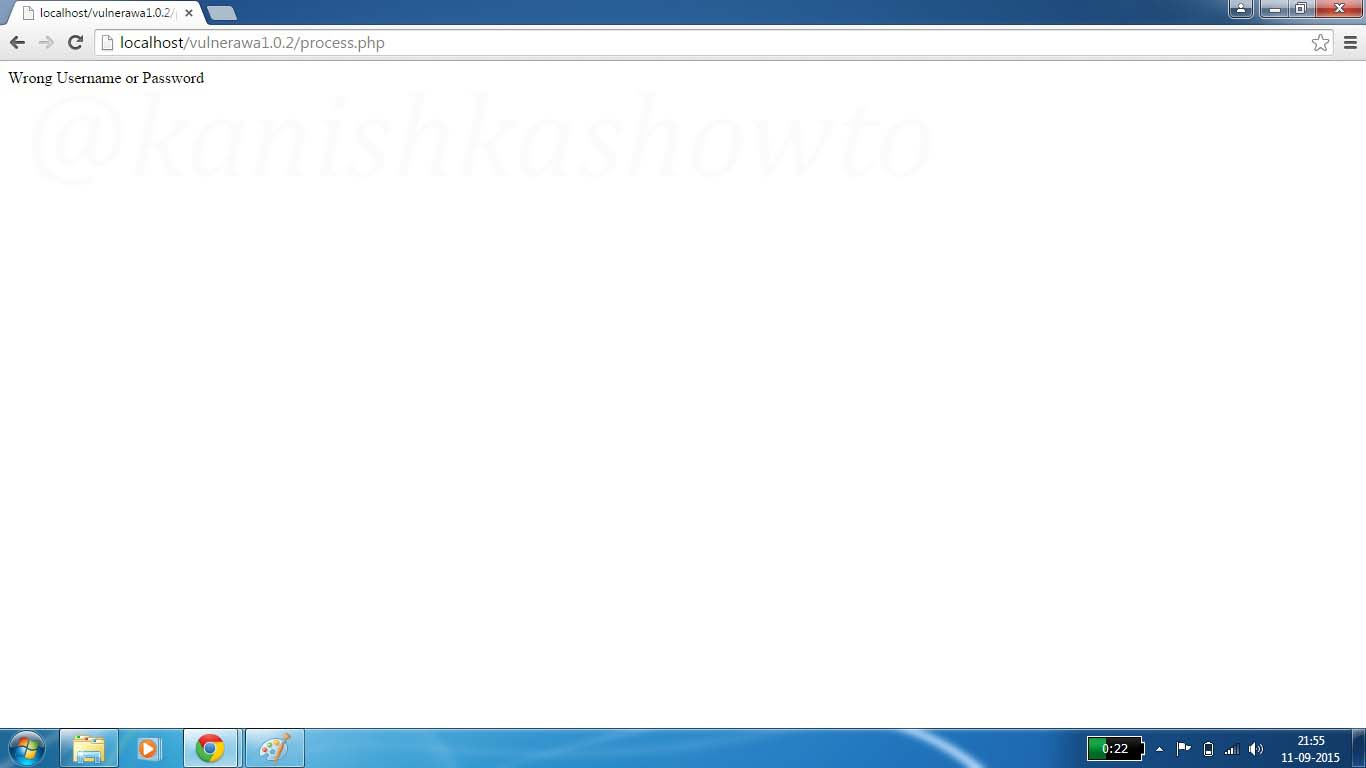
The “mysqli_real_escape_string” escapes any escapes any special characters entered in the input fields thus rendering injection harmless.
Follow Us

Great article, very clearly written with excellent screenshots !
Thanks
What’s the point in writing a blog post about the most basic SQLi and being pretentious enough to quote the Art of War! Hahahaha.
Nice article, congrats.
Thank you very much, Cereal.
Brilliant Tutorial on Detection and Prevention of Sql Injection Attack
“Surprisingly, he gets access to the restricted area….”<==Referring to this line,can you create the php mysql code to get access to the resticted area like to retrieve sensitive user information and mail me the code asap
haha,
works like a charm. tried it on http://www.sticktipp.de
define(‘DB_NAME’, ‘db479035460’);
/** Ersetze username_here mit deinem MySQL-Datenbank-Benutzernamen */
define(‘DB_USER’, ‘dbo479035460’);
/** Ersetze password_here mit deinem MySQL-Passwort */
define(‘DB_PASSWORD’, ‘st1ckt1pp’);
/** Ersetze localhost mit der MySQL-Serveradresse */
define(‘DB_HOST’, ‘db479035460.db.1and1.com’);
/** Der Datenbankzeichensatz der beim Erstellen der Datenbanktabellen verwendet werden soll */
define(‘DB_CHARSET’, ‘utf8’);
/** Der collate type sollte nicht geändert werden */
define(‘DB_COLLATE’, ”);
can we bypass router login page its username and password
Ishwor, it depends. But mostly router logins can be bypassed using default username and passwords.
Attacks on website is very common now a days. You blog is surely help us to maintain our website security and make safe them.Thanks for the article.
You are welcome, Phpprogrammer.
[…] 5. Login Bypass using SQL Injection – Hackercool Magazine […]
[…] 4. Login Bypass using SQL Injection – Hackercool Magazine […]