Good Evening friends. Today we will see a step by step guide on how to create a web application penetration testing lab .
For creating this lab, I am using a host machine with Windows 7 installed on it. We also need the following software.
1. Wamp server ( Download here)
2. Vulnerawa ( Download here )
3. Vmware Workstation or Oracle Virtualbox ( Download here )
4. Kali Linux ( Download here )
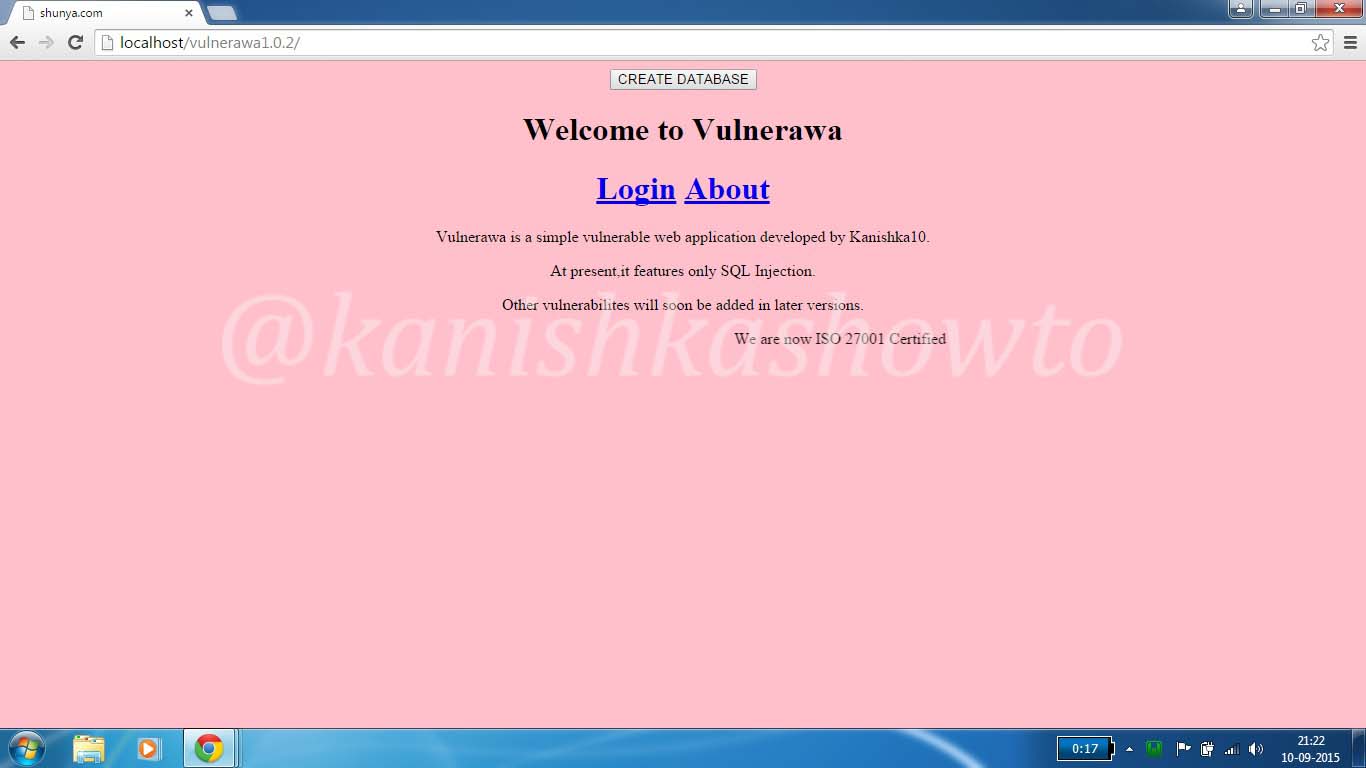
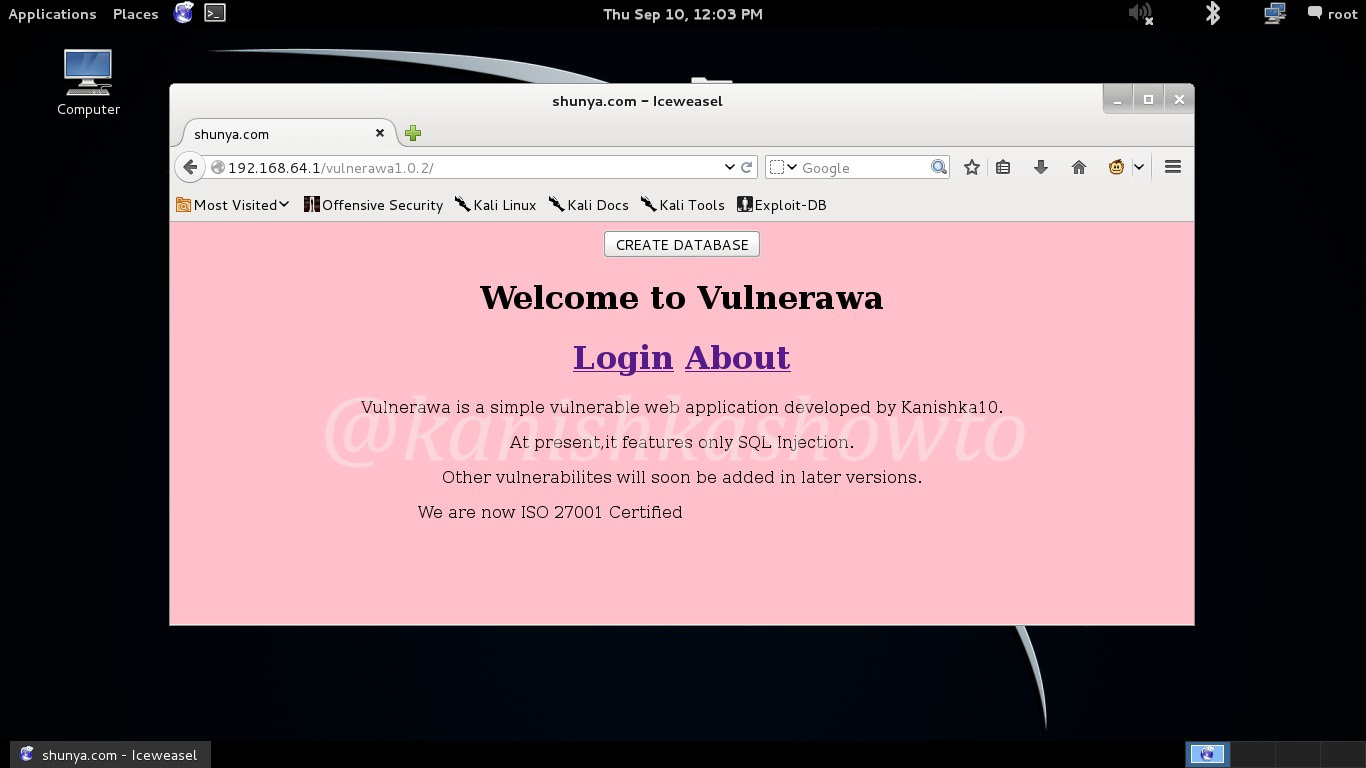
Download the above software to your system. Install Wamp server. For this WAPT lab, we will use Vulnerawa as a vulnerable website or target website. Extract the contents of the vulnerawa.zip folder to the root folder of the Wamp server. Now open a browser and and type localhost in the URL bar to see if you can see the victim webapp as shown below.
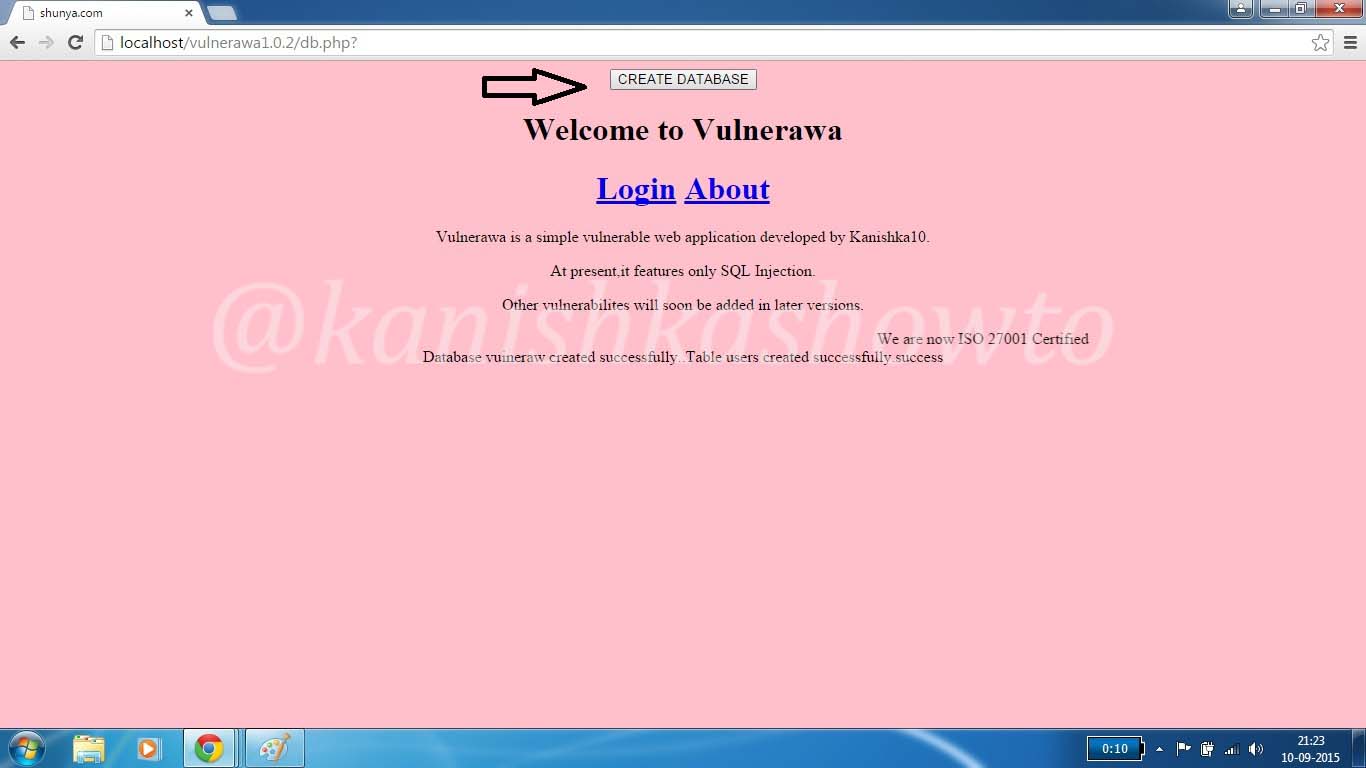
Click on “Create Database” to create some data which we will use in our future howto’s.
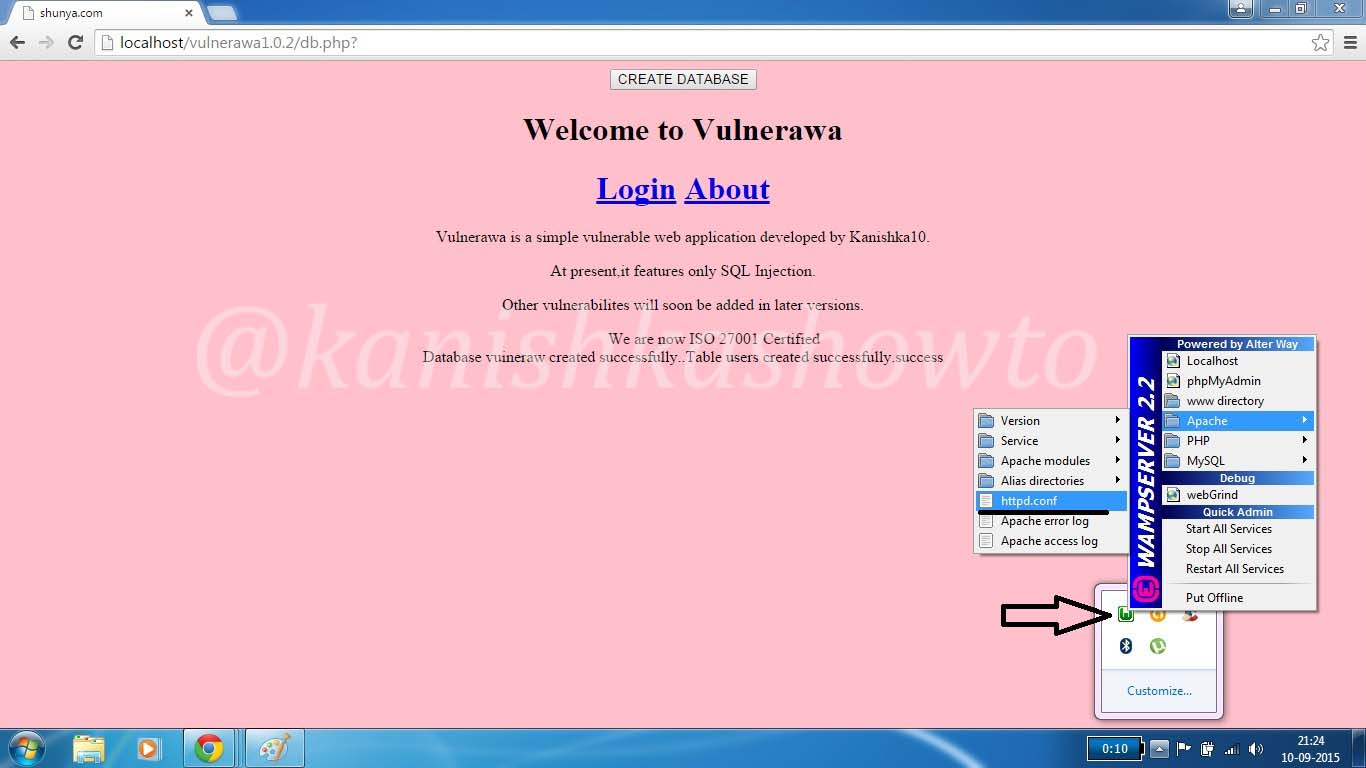
Now let’s change the permissions of the Wamp server to access it from our attacker machine. Go to Apache>httpd.conf as shown below.
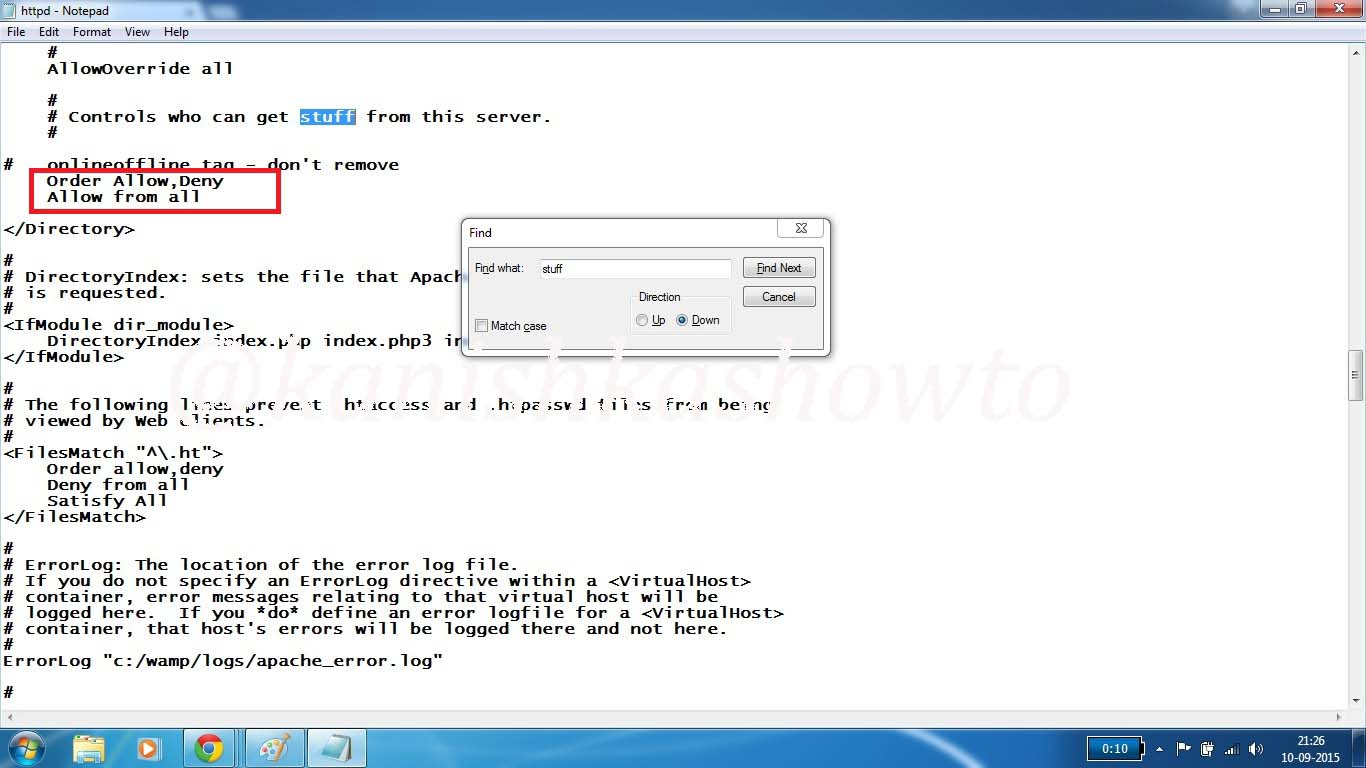
You should see the httpd.conf as shown below. Type CTRL+F and search for word “stuff”. After you find it, make changes as shown below in the red box. Save the file by typing CTRL+S and restart the Wamp server.
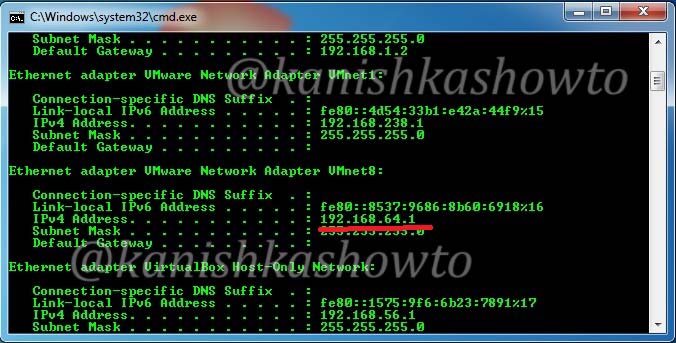
Now install Kali Linux in Vmware Workstation or Oracle Virtualbox (see how ). Set the network adapter to NAT. Now open command line in your host machine and check the IP address assigned to your host machine as shown below by typing command “ipconfig”. Since I am using Vmware Workstation my network adapter is Vmware network adapter vmnet8. The IP address assigned to my host machine is 192.168.64.1.
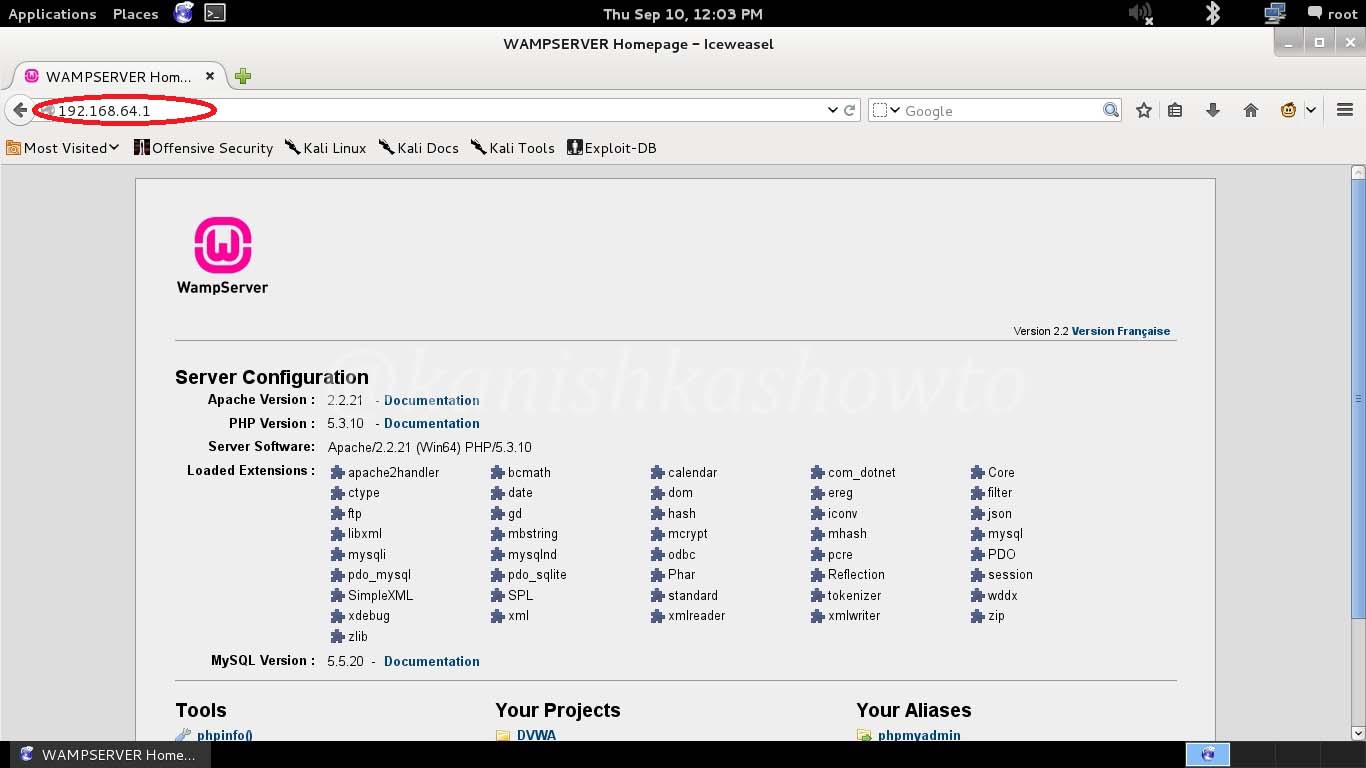
Now start your attacker machine( Kali Linux ), open browser and type the address 192.168.64.1 in the url bar and see if you can access the victim web application as shown below.
Your web application penetration testing lab is ready. Happy hacking practice.
Follow Us

[…] Hi Friends. Today we will see how to perform SQL injection with sqlmap. Sqlmap is an “open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers “. It is pre-installed in Kali Linux. For this tutorial I am using Vulnerawa as target and it is necessary to setup a webapp pentest lab with it. See how to set up a webapp pentest lab. […]