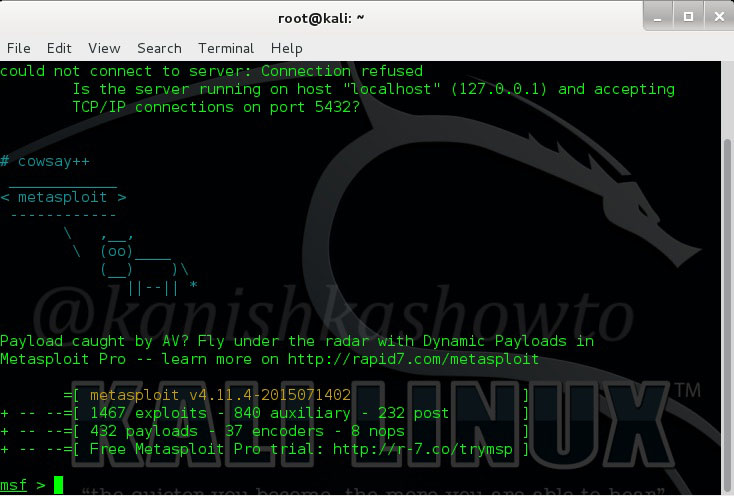
Good Evening friends. Today we will see how to add new exploits to Metasploit from the exploit database. As we all know, Metasploit is a framework to exploit systems. This howto is being done in Kali Linux which has Metasploit installed by default. You can see below that here Metasploit has total 1467 exploits. Now let us add the recently released Microsoft Windows Media Center MCL vulnerability exploit to Metasploit framework.
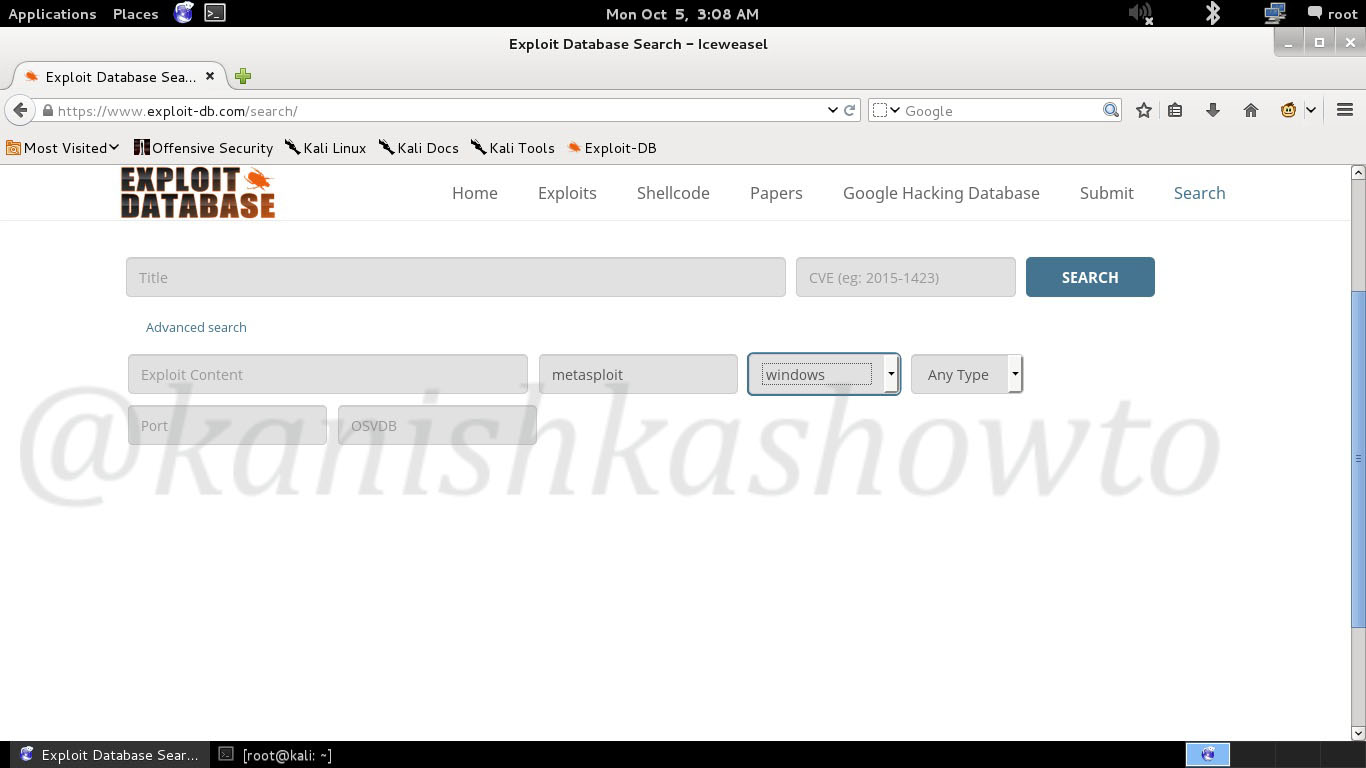
Go to the website exploit-db.com and open the search option as shown below. Go to the Advanced Search option and give the below values to search for all the exploits for Metasploit.
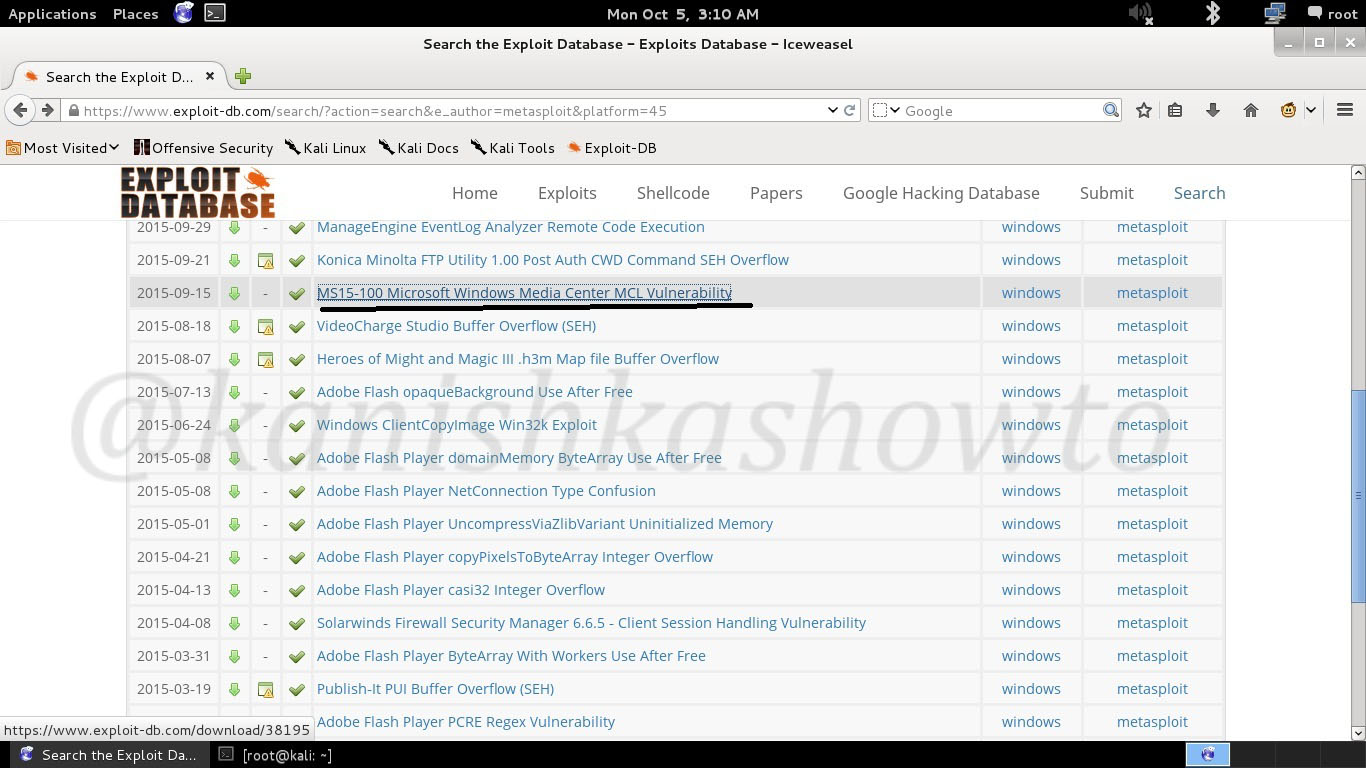
As the below image shows, we get all the exploits authored by Metasploit. We are interested in the Ms15-100 Microsoft Windows Media Center MCL vulnerability underlined below.
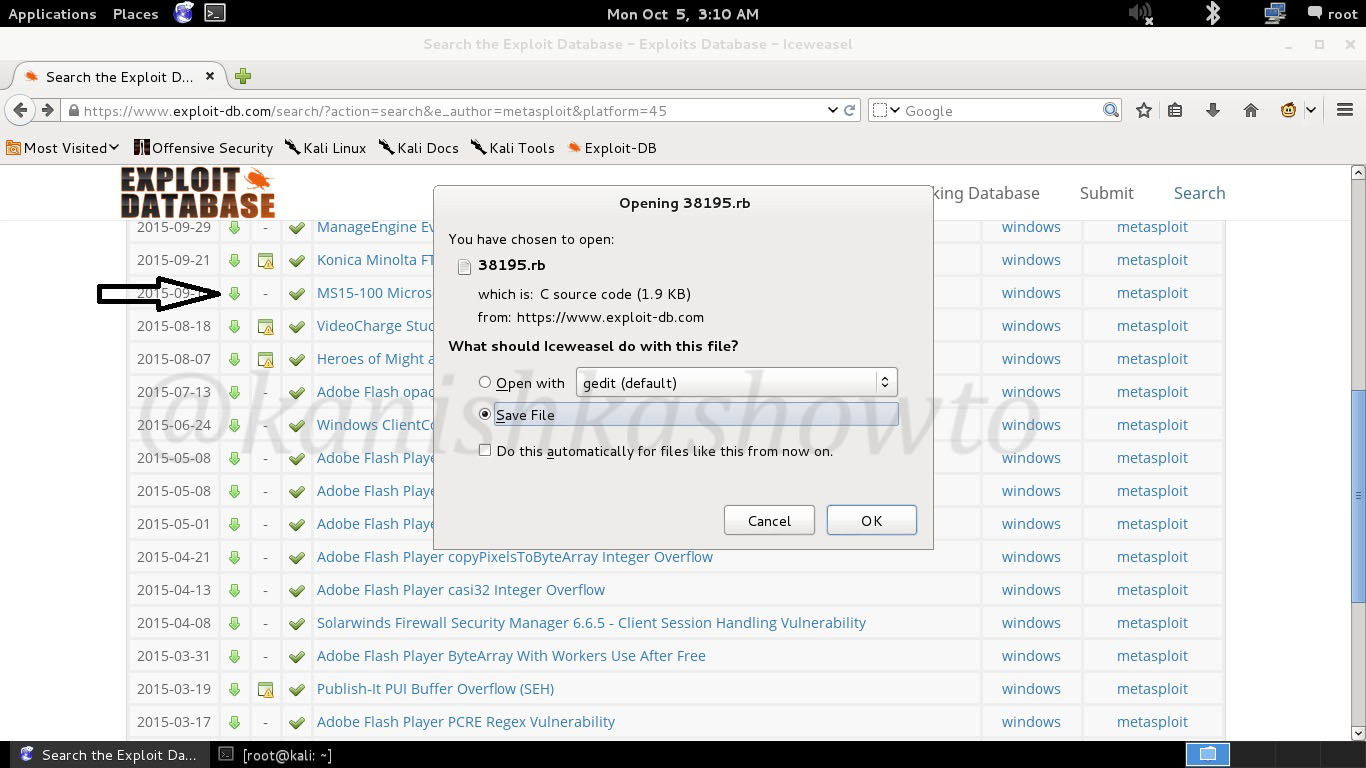
Now click on the download option as shown below. A window will open as shown below. Select the Save option.
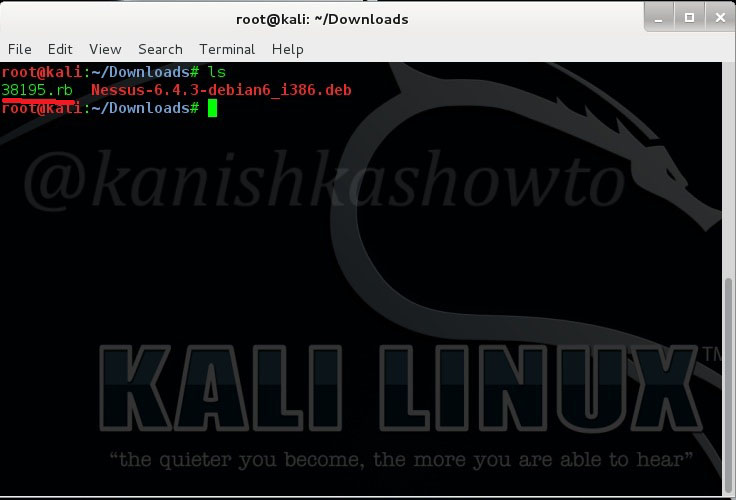
Now open a terminal and navigate to the Downloads folder to check your download. In our present case it is “38195.rb”.
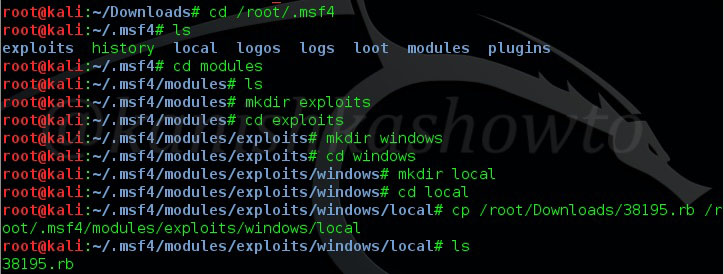
Now navigate to the directory where metasploit stores its exploits by typing command “cd/root/.msf4“. Go into modules directory and create a directory named “exploits” inside that directory. Now go into the exploits directory(which you just created) and create another directory named “windows”, inside the windows directory( which once again you just created) create directory “local”. If you are getting confused, all the steps are given in below image, just follow them. We are just creating a valid path for metasploit to find this exploit. Once you are in the local directory, copy the exploit you just downloaded to the local folder as shown below.
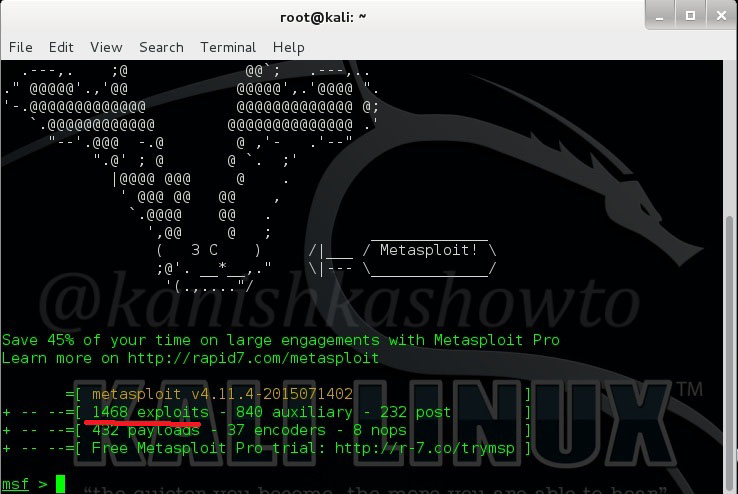
Ok, we’re almost done. Now restart the system and fire up your Metasploit. Now you can see that we have 1468 exploits as 1467 previously.
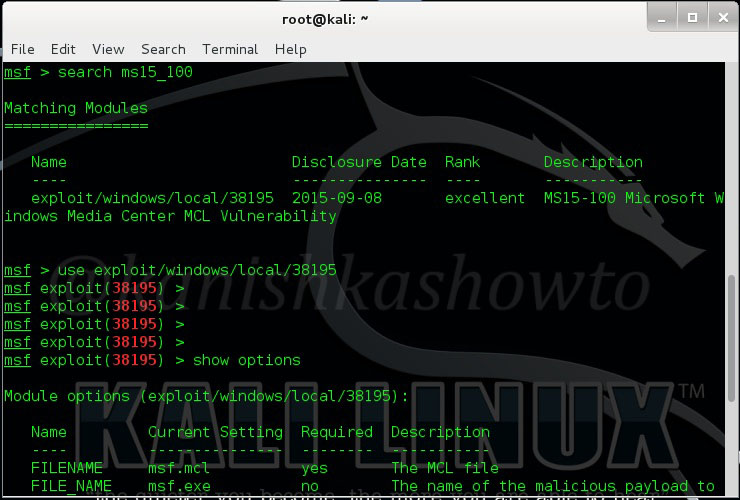
Now let us search for our exploit by typing command “search ms15_100”. Load the exploit as shown below. We have successfully added a new exploit to Metasploit. Hope that was helpful.


Didn’t worked for me i tryed reload_all also …
any suggestions ?
Dave what is the exact error you are getting? Can you please tell me.
I don’t receive any errors i just cant see the new exploit loaded i will mention i use Kali 2.0 and metasploit-framework 4.11
root@kali:~# cd/root/.msf4
bash: cd/root/.msf4: No such file or directory
@Mario, give space between ‘cd’ and ‘/root/.msf4/’. Remember Linux is very strict.
I have the following errors any idea:
from /usr/share/metasploit-framework/modules/exploits/windows/local/40085.rb) due to Missing compatible Metasploit class constant
@Gardener, can I know what exploit are you trying to add to Metasploit.
Issue solved long ago thank you all.
@susmith HCK. For exploits to work in Metasploit, they have to be ported to ruby.
how to use exploit-db?? i don’t get this
@kalilinuxhack. What exactly are you unable to understand here.
Hi. I googled importing of exploits from exploit-db to MSF. But all examples are ruby scripts. I tried to import python .py scripts, then i performed Search on MSF prompt but the added .py exploit did not appear in the Search results. I tried both (1)/root/msf4/modules and (2) /usr/share/metasploit-framework/modules/. Both without success. How do we import python scripts from exploit-db into metasploit?
Hello Marko, Metasploit is entirely coded in Ruby and at present it only supports Ruby exploits.It doesn’t support modules or scripts written in Python. This is the reason why python exploits do not appear in Metasploit search results.
Welcome brother.